Zscaler Zero Trust Network Access: What It Is & Benefits


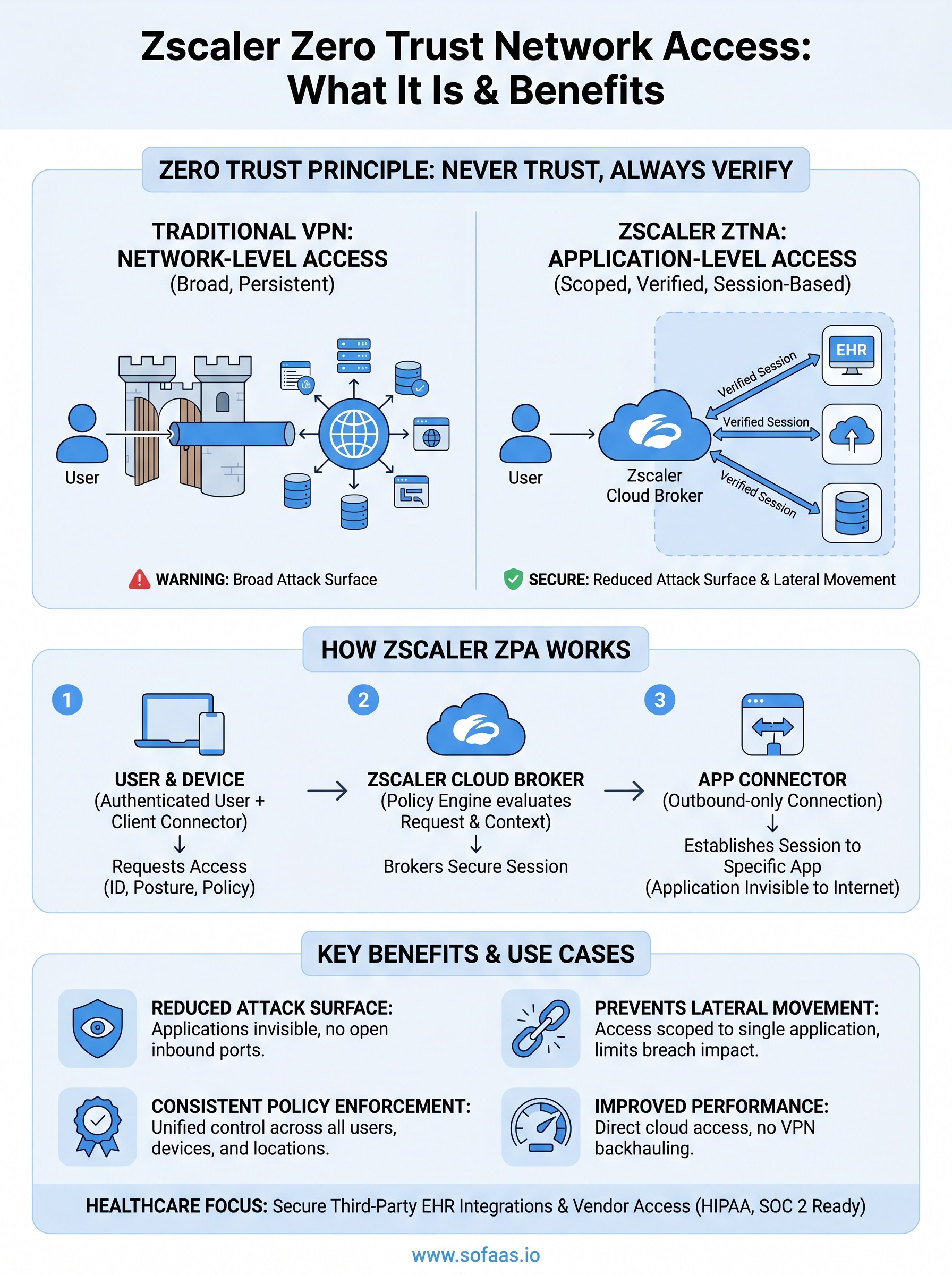
Traditional VPNs were built for a different era, one where users, applications, and data all lived inside a corporate perimeter. That perimeter no longer exists. Remote workforces, cloud-hosted applications, and distributed architectures have made perimeter-based security a liability rather than an asset. Zscaler Zero Trust Network Access (ZTNA) replaces that outdated model with one built on a simple principle: never trust, always verify.
For healthcare organizations connecting third-party applications to EHRs, something we handle every day at SoFaaS, zero trust isn't optional. Patient data flows between applications, providers, and cloud infrastructure constantly, and every connection point is a potential attack surface. Our platform enforces HIPAA-compliant, SOC 2 Type II-certified security across every integration, and that philosophy aligns directly with what Zscaler's ZTNA architecture aims to accomplish at the network access layer.
This article breaks down what Zscaler Zero Trust Network Access actually is, how its flagship product Zscaler Private Access (ZPA) works under the hood, and why organizations are replacing legacy VPNs with it. You'll get a clear picture of the core benefits, implementation considerations, and where ZTNA fits within a broader security strategy, whether you're evaluating it for general enterprise use or specifically for environments handling sensitive healthcare data.
What Zscaler ZTNA is and what it is not
Zero trust is an access philosophy, not a product you install once and forget. At its core, it operates on one rule: no user, device, or application earns implicit trust, regardless of where the connection originates. Zscaler zero trust network access operationalizes this principle at the network layer, giving you control over exactly which users can reach which applications without placing those users on the broader corporate network.
What ZTNA actually is
Zscaler ZTNA is a software-defined access model that connects authenticated users directly to specific applications rather than to network segments. Instead of routing traffic through a corporate firewall or VPN concentrator, it uses cloud-based broker connections positioned between users and applications. When a user requests access, the system evaluates identity, device posture, and contextual signals before allowing a precise, application-level connection.

This architecture means the application itself stays invisible to unauthenticated users because it never appears on the public internet. The broker facilitates a connection only after confirming the request meets your defined policies. Contextual factors such as device health, user role, geographic location, and time of access all influence the decision. You gain granular control over who reaches what, and that access terminates the moment the session ends rather than leaving a persistent tunnel open.
With ZTNA, the network is no longer the perimeter. The application becomes its own enforced boundary.
What ZTNA is not
ZTNA is not a firewall, antivirus tool, or endpoint protection platform. It does not scan files, detect malware signatures, or replace your identity provider. Its function is specifically access control and connectivity, determining whether a verified user can reach a specific application. Conflating it with a broader security suite leads to real gaps in your architecture.
ZTNA is also not a complete replacement for every security control you currently run. Identity and device management tools still need to feed signals into the ZTNA broker for contextual decisions to work accurately. Your endpoint detection tools still assess device health independently. ZTNA acts as the policy enforcement point for network access, sitting on top of those signals rather than generating them itself.
The ZTNA versus zero trust architecture distinction
A common misconception is that ZTNA and zero trust architecture (ZTA) are interchangeable. Zero trust is a broader strategic framework covering data access, lateral movement controls, identity governance, and workload security. ZTNA handles the network access component of that framework and nothing more. If you deploy Zscaler ZPA but leave internal lateral movement unchecked and data access unmonitored, you have one piece of zero trust in place, not a complete zero trust posture. Knowing that boundary helps you build a security strategy where each layer covers what the others do not.
Why ZTNA matters for modern access
The way people work has fundamentally changed, and the access models built to support them have not kept pace. Users now connect from home networks, branch offices, and mobile devices rather than from a controlled office environment. Applications live in AWS, Azure, and SaaS platforms rather than in on-premises data centers your firewall once protected. That shift dismantles every assumption traditional perimeter security relied on, and organizations that have not updated their access architecture are operating with significant, measurable exposure.
The collapse of the network perimeter
For decades, organizations drew a hard line between inside and outside. Put a user inside that perimeter and they could reach everything the network offered. That model assumed threats came from the outside, and it assumed users and devices already inside were inherently safe. Neither assumption holds anymore. Attackers regularly exploit compromised credentials to move laterally through internal networks once they clear the perimeter, often going undetected for weeks. Legacy remote access tools extend that trusted zone to every device a user connects from, regardless of whether that device is patched or compromised.
When you put users on your network instead of connecting them to specific applications, you hand attackers the same broad access your employees have.
Why application-level access reduces real risk
Zscaler zero trust network access solves this by never placing users on the broader network in the first place. Each session connects a verified user directly to a specific application and nothing beyond that target. If a credential is compromised, the attacker gains access only to what that session authorized, not to adjacent systems, databases, or services running alongside it. Scoping access to the application level directly limits how much damage a compromised account can cause, and that outcome is one perimeter-based tools structurally cannot replicate.
Healthcare organizations feel this pressure acutely because regulated patient data moves across multiple application layers involving many vendors and connection types. A single misconfigured access path or over-permissioned segment can trigger HIPAA violations, breach notifications, and significant penalties. Applying strict, verified, application-level access policies for every connection reduces the surface area available to anyone attempting to move laterally through your environment.
How Zscaler ZTNA works with Zscaler Private Access ZPA
Zscaler Private Access (ZPA) is Zscaler's primary product for delivering zscaler zero trust network access in practice. It handles the mechanics of brokering secure, application-level connections without ever placing users on the corporate network. Understanding how ZPA operates under the hood gives you a clear view of why the architecture performs the way it does.
The broker model explained
ZPA uses a cloud-based intermediary called the Zscaler cloud to sit between your users and your applications. Your applications connect outbound to the Zscaler cloud through a lightweight component called the App Connector, which you deploy on-premises or in your cloud environment. That connector establishes an outbound-only tunnel, meaning your applications never need inbound firewall ports opened and never appear directly reachable from the internet.
Because the application initiates the outbound connection rather than the user, attackers scanning the public internet cannot discover or probe the application at all.
Users connect through Zscaler Client Connector, an agent installed on their device, which authenticates them against your identity provider before forwarding the access request to the Zscaler cloud. The cloud then evaluates the request against your defined policies, checks device posture signals, and either brokers the connection or denies it. No direct network path ever forms between the user and your infrastructure.
What happens during a ZPA session
When a verified user requests access, ZPA stitches together a secure, encrypted session between the user-side connector and the App Connector on the application side. The connection stays scoped to that specific application for the duration of the session. Once the session ends, the connection closes completely, leaving no persistent tunnel a threat actor could reuse or exploit later.
Each session decision factors in identity signals from your identity provider, device health status, user role, and any location or time-based policies you configure. You control all of those policy definitions through the ZPA admin portal, where you map specific users or groups to specific applications and define exactly what conditions must be true before a session is brokered.
ZTNA vs VPN in plain terms
Both technologies solve the same problem on the surface: give users outside your office access to internal resources. The difference lies in how they solve it, and that difference has serious security consequences. A VPN creates a network tunnel; ZTNA creates an application-level connection. Those two approaches produce completely different risk profiles once you put them under any real scrutiny.
What a VPN actually does
A VPN places a remote user directly onto your network as if they were sitting inside your office. Once connected, that user can see and potentially reach anything the network segment allows, servers, databases, shared drives, and adjacent applications included. Network-level trust is granted at authentication, and it persists for the entire session. You get one decision point, one gate, and broad access on the other side of it.
Once a VPN grants access to the network, it cannot easily limit where that access goes without additional segmentation tools layered on top.
Where VPNs break down
VPNs were designed for a world where a small number of trusted employees occasionally connected remotely to an otherwise on-premises environment. That world no longer exists for most organizations. When hundreds of users connect from unmanaged home devices across unreliable networks, the VPN model exposes your entire internal environment to every compromised credential or infected endpoint in that group. Attackers who steal a valid VPN credential gain the same broad access your employees have, and lateral movement through your internal network becomes straightforward.
Performance is a secondary but real issue. Backhauling user traffic through a central VPN concentrator before routing it to a cloud application adds latency that frustrates users and degrades productivity at scale.
How zscaler zero trust network access changes the comparison
Zscaler ZTNA never places users on your network. Instead of a tunnel to the network, ZPA brokers a session to one specific application after verifying identity, device posture, and policy. A compromised credential reaches one application target, not your entire internal environment. Each session is scoped, verified, and closed when the user disconnects, eliminating the persistent tunnel that makes VPN credentials so valuable to attackers. You get the same connectivity outcome with a fraction of the attack surface.
Key benefits and common use cases for Zscaler ZTNA
Understanding the architecture is useful, but what matters operationally is what zscaler zero trust network access actually delivers in your environment. The benefits are concrete and measurable, not theoretical, and the use cases span industries from healthcare to financial services to distributed retail.
Core security and operational benefits
Deploying Zscaler ZPA reduces your attack surface at the infrastructure level by making your internal applications invisible to the public internet. Because the App Connector initiates outbound-only connections, there are no open inbound ports for attackers to probe or exploit. You remove entire categories of risk simply by changing how connectivity works.
Shrinking your publicly exposed attack surface is one of the highest-value security improvements you can make without touching your application code.
Lateral movement becomes structurally harder because users never land on your network segment. If a credential is stolen, the attacker reaches one application, not the adjacent systems running alongside it. You also gain consistent policy enforcement across every user and device type, whether your workforce connects from managed laptops, personal devices, or third-party contractor machines, without maintaining separate VPN configurations for each group.
Common use cases where ZTNA fits well
Remote workforce access is the most common starting point. Replacing legacy VPN infrastructure with ZPA gives distributed teams lower latency access to internal applications without backhauling traffic through a central concentrator. Organizations with heavy cloud application usage see immediate performance improvements.
Third-party and vendor access management is a strong secondary use case. Contractors and partners typically need access to one or two specific tools, not your entire environment. ZPA lets you scope their sessions precisely, grant time-limited access, and revoke it instantly without modifying firewall rules or managing shared credentials. For healthcare organizations specifically, this applies directly to third-party application integrations with EHR systems, where precise, auditable access control is both a security requirement and a compliance obligation. Each vendor connection stays bounded, verified, and logged, which satisfies audit requirements without adding manual overhead to your security team.
Where to go from here
Zscaler zero trust network access gives you a concrete way to move beyond perimeter-based security and enforce application-level access controls that actually match how modern workforces operate. You now understand the architecture, how ZPA brokers connections, where VPNs fall short, and which use cases deliver the clearest return. The next step is applying that thinking to your own environment and identifying which access paths carry the most risk today.
For healthcare organizations managing EHR integrations and third-party application access, the same zero trust principles apply directly to how your data moves between systems. Every vendor connection, every API call, and every patient data exchange benefits from verified, scoped, and auditable access controls. If you are building or scaling a healthcare application that needs to connect with EHR systems securely and efficiently, launch your SMART on FHIR integration with SoFaaS and see how a managed, compliance-ready platform removes that complexity from your team entirely.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.