Vanta SOC 2 Compliance: Costs, Setup, And What To Expect


Vanta SOC 2 Compliance: Costs, Setup, And What To Expect
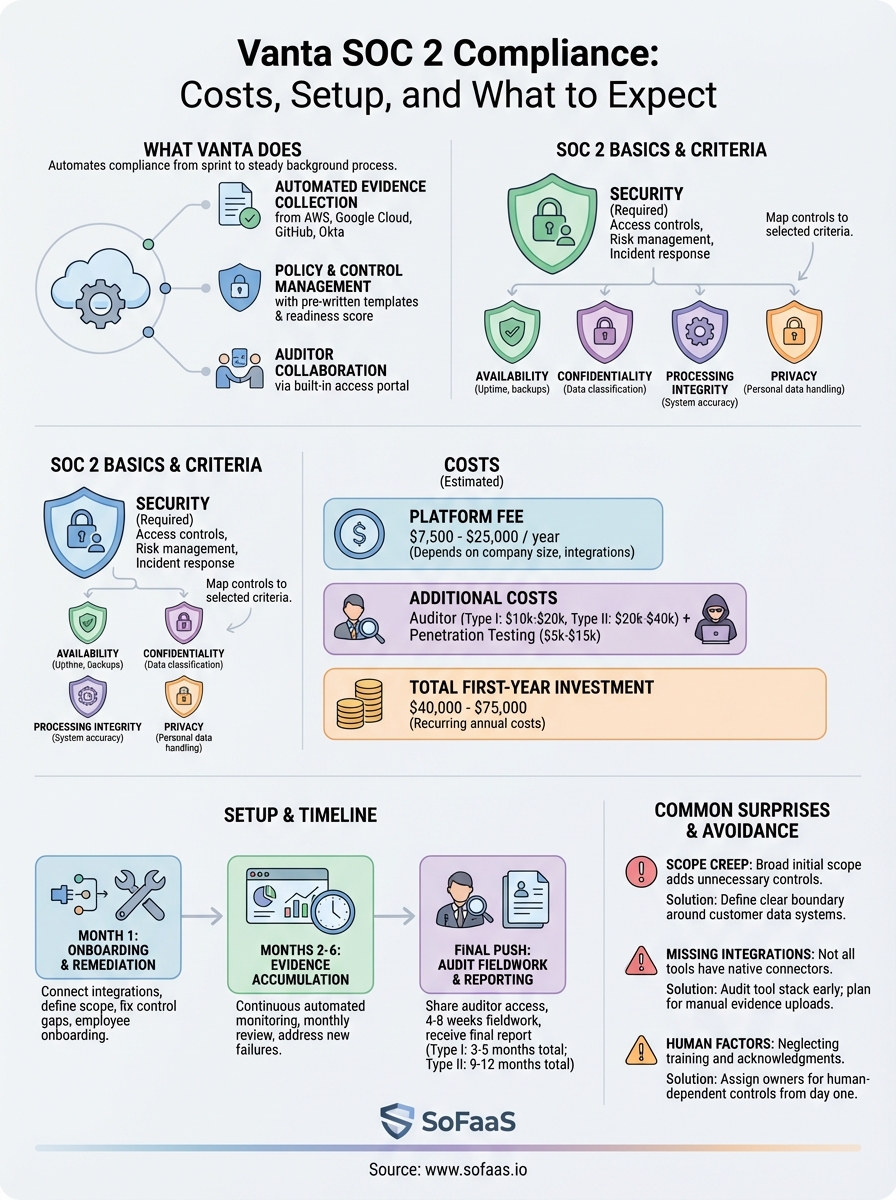
Getting SOC 2 certified is one of those things that sounds straightforward until you actually start doing it. There are policies to write, evidence to collect, controls to implement, and auditors to satisfy, and most teams underestimate how much work goes into all of it. That's exactly why tools like Vanta exist. Vanta SOC 2 compliance automation has become a go-to choice for companies that want to streamline the process, but knowing what it actually costs, how setup works, and what the experience looks like day-to-day requires more than a glance at a pricing page.
We built SoFaaS on SOC 2 Type II compliant infrastructure because healthcare data integration demands it. Our platform handles sensitive patient information flowing between EHR systems and third-party applications, so earning and maintaining that certification wasn't optional, it was foundational. That process gave us firsthand exposure to compliance tooling, audit prep, and the real costs involved in getting SOC 2 done right.
This article breaks down what you can expect from using Vanta for SOC 2 compliance: the actual costs (beyond the sticker price), what setup and onboarding look like, how the platform works once you're in it, and where it fits compared to doing things manually or choosing a different tool. Whether you're a healthcare startup preparing for your first audit or a growing company maintaining an existing certification, this guide covers what you need to make an informed decision.
What Vanta does for SOC 2 compliance
Vanta is a compliance automation platform that connects to your infrastructure, monitors your controls continuously, and builds the evidence library your auditor needs to issue a SOC 2 report. Instead of manually pulling screenshots, writing policies from scratch, and tracking down access logs before an audit, Vanta pulls that data automatically from integrations with cloud providers, identity systems, HR platforms, and developer tools. The platform turns compliance from a sprint into a steady background process, which is a meaningful shift for any team running lean.
Automated evidence collection
The biggest time sink in any SOC 2 audit is evidence collection, meaning the work of proving that your controls actually operated as intended over the audit period. Vanta handles this by connecting directly to your existing tools through pre-built integrations. It links to platforms like AWS, Google Cloud, GitHub, and Okta, then continuously pulls data confirming that encryption is enabled, access reviews are completed on schedule, and employee background checks are documented. Each integration feeds into a central dashboard, so you can see at a glance which controls are passing and which need attention.

This automated approach matters because auditors require current and continuous evidence, not a point-in-time snapshot assembled under pressure in the weeks before fieldwork begins. Vanta captures evidence on an ongoing basis. When your auditor asks for 12 months of proof that you reviewed user access permissions quarterly, that data already exists in your Vanta account. You are not reconstructing history, explaining gaps, or hoping your team saved the right screenshots.
The difference between a clean audit and a stressful one often comes down to whether evidence collection was continuous throughout the year or rushed in the final month.
Policy and control management
Beyond evidence, Vanta gives you a library of pre-written policy templates covering the most common SOC 2 requirements. These templates are not generic boilerplate you copy and paste without thinking. They are designed to align with specific Trust Services Criteria so that when an auditor reviews them, each policy maps directly to the controls your report needs to address. You customize them to reflect how your organization actually operates, then publish them inside the platform and track employee acknowledgments automatically.
Control management works on the same principle. Vanta maps your connected tools and configurations to specific SOC 2 control requirements, then flags gaps where a control is not yet implemented or where evidence is missing. You get a live readiness score, which makes it easier to prioritize remediation work and report progress to leadership without building a manual tracking spreadsheet every week.
Auditor collaboration
Vanta includes a built-in auditor access portal that lets your CPA firm log into a read-only view of your evidence and controls directly inside the platform. This removes the back-and-forth of exporting documents, creating zip files, and emailing attachments every time your auditor has a follow-up question. Your audit fieldwork moves faster because the auditor can review evidence independently while your team focuses on resolving any open findings rather than fielding document requests.
For teams pursuing Vanta SOC 2 compliance, this auditor workflow is one of the more underappreciated features. Auditors who have worked with Vanta before already know how to navigate the interface, which means less time orienting them and more time making forward progress on the report itself. Choosing an auditor who is already familiar with the platform is worth asking about during your initial conversations with audit firms.
SOC 2 basics Vanta will ask you to prove
SOC 2 is built around five Trust Services Criteria: Security, Availability, Confidentiality, Processing Integrity, and Privacy. Security is the only required category; the rest are optional depending on what your customers expect and what your product promises. Before Vanta can automate your evidence collection, you need to understand which controls fall under each category you're pursuing, because the platform can only gather evidence for controls that actually exist in your environment.
The Security category covers the most ground
Security, also called the Common Criteria, is where the bulk of SOC 2 work lives. It covers logical and physical access controls, risk management, change management, incident response, and vendor management. Vanta maps these requirements to specific configurations in your connected systems, such as whether multi-factor authentication is enforced across your identity provider or whether production access is restricted to authorized personnel only.
Your access control and identity management practices will receive the most auditor scrutiny. You need to show that you review who has access to sensitive systems on a regular schedule, that terminated employees lose access promptly, and that privileged access is both limited and logged. Vanta tracks these controls continuously and flags lapses so you can fix them before an auditor finds them.
Getting your access review process right before your audit period starts saves more time than almost any other preparation step.
Availability and confidentiality require documented commitments
If your product includes availability or confidentiality commitments, those categories add specific controls you need to prove. Availability covers uptime monitoring, backup procedures, and incident response plans. Confidentiality covers how you identify, classify, and protect sensitive data throughout its lifecycle. Neither category is complicated to address with the right tooling, but both require that you have the processes in place before Vanta can collect evidence for them.
Vanta SOC 2 compliance tooling makes this clearer by showing you exactly which controls apply to the categories you have selected. You are not guessing what an auditor will ask for. The platform surfaces specific requirements, connects them to your infrastructure, and tells you what is missing so your team can close gaps methodically rather than reactively. Knowing this before you start onboarding saves you from discovering large control gaps only weeks before your scheduled audit fieldwork.
How much Vanta costs for SOC 2
Vanta does not publish fixed pricing publicly, which means the number you pay depends on your company size, the number of integrations you need, and the compliance frameworks you want to cover. Most companies pursuing Vanta SOC 2 compliance for a single framework pay somewhere between $7,500 and $25,000 per year, based on widely reported estimates from users who have shared their experiences. The actual quote you receive will vary, and Vanta's sales team typically starts with a discovery call to scope your environment before giving you a number.
What drives your quote up
Several factors push the annual cost higher. The number of employees at your company is the primary pricing driver, since Vanta prices partly based on headcount. Beyond that, adding frameworks beyond Security-only SOC 2, such as HIPAA or ISO 27001, adds to the base cost. Integration volume also matters; connecting more cloud providers, SaaS tools, and identity platforms increases the scope of what Vanta monitors and prices accordingly.
If your organization operates in healthcare or handles regulated data, you may find yourself adding HIPAA compliance on top of SOC 2 from the start. That combination is common but adds cost, so factor it into your budget conversations early rather than discovering it mid-negotiation.
Asking Vanta specifically what triggers pricing tiers before your first call puts you in a better position to compare quotes accurately.
The cost beyond the platform fee
The platform fee is not your total SOC 2 cost. You also need to budget for an independent auditor, since Vanta does not conduct audits itself; it prepares you for one. A Type I audit typically runs between $10,000 and $20,000, while a Type II audit from a reputable CPA firm often lands between $20,000 and $40,000 depending on scope and auditor reputation. Penetration testing, which most auditors expect to see for the Security category, adds another $5,000 to $15,000 depending on the vendor and the scope of your environment.

Your total first-year investment for SOC 2 using Vanta routinely falls between $40,000 and $75,000 when you include the platform, the audit, and any required testing. Renewal years cost less because you are not starting from scratch, but the platform subscription and audit fees recur annually, so plan for ongoing spend rather than treating certification as a one-time expense.
How to set up Vanta for a SOC 2 audit
Setting up Vanta SOC 2 compliance starts before you open the platform. Before your first login, you need to define your audit scope: which systems handle sensitive data, which Trust Services Criteria you are pursuing, and roughly when you want your audit to begin. Walking into onboarding without those decisions made slows you down, because every configuration step Vanta asks you to complete depends on knowing what you are trying to prove and to whom.
Connect your integrations first
Your first action inside Vanta is connecting the tools your company already uses. Vanta's integration library covers cloud infrastructure providers like AWS, Azure, and Google Cloud, along with identity providers, HR systems, code repositories, and endpoint management tools. Each connection you complete allows the platform to start pulling evidence automatically rather than waiting for you to upload it manually.
Prioritize the integrations that touch the most sensitive data in your environment first. If your product runs on AWS and your team authenticates through Okta, those two connections alone unlock a large portion of the evidence Vanta needs for Security controls. Work through the remaining integrations methodically based on which controls they support, and flag any tool that lacks a native Vanta integration early, since those gaps require manual evidence uploads.
The integrations you complete in week one determine how much automated evidence Vanta can collect for the rest of your audit period, so treat that step as your highest priority.
Configure your scope and controls
Once your integrations are live, Vanta surfaces a control library mapped to SOC 2 requirements and flags which controls are passing, failing, or not yet addressed. Work through each failing control and assign it to the team member responsible for remediation. Some controls resolve automatically once you enforce a setting in a connected tool; others require a policy document or a manual process your team needs to build.
Scope configuration also covers which systems and services fall inside your audit boundary. Limiting scope to only the systems that handle customer data reduces the number of controls you need to satisfy and lowers the complexity of your audit. Your auditor will review this scoping decision, so document your reasoning clearly inside the platform.
Complete employee onboarding inside the platform
Vanta tracks security training completion and policy acknowledgments for every employee, which auditors expect to see as part of your Security controls. Add your full team to the platform early so those completion records accumulate over time rather than being rushed in the final weeks before fieldwork. Employees receive automated reminders, which removes the burden of chasing acknowledgments manually and keeps your compliance readiness score accurate throughout the year.
What the SOC 2 timeline looks like with Vanta
The total time from starting Vanta to receiving a completed SOC 2 report depends on which report type you pursue and how much remediation work your environment needs. A Type I report, which captures your controls at a single point in time, typically takes three to five months from initial setup. A Type II report, which covers a defined audit period of at least six months, runs nine to twelve months for most companies going through the process for the first time.

The first 30 days: onboarding and gap remediation
Your first month inside Vanta SOC 2 compliance tooling is almost entirely remediation work. Once you connect your integrations, the platform surfaces failing controls immediately. Some of those failures are quick fixes, such as enforcing MFA across your identity provider or enabling encryption on a storage bucket. Others take longer because they require you to build a process, assign an owner, and let that process run before evidence starts accumulating. Budget your first 30 days primarily for closing control gaps rather than expecting to enter audit fieldwork quickly.
Your team's remediation pace during this window sets the ceiling on how fast you can move. Assigning each failing control to a specific owner on day one, rather than leaving ownership ambiguous, is the single most effective thing you can do to keep the project on schedule.
Months two through six: evidence accumulation
Once your controls pass inside Vanta, the platform starts building the continuous evidence record your auditor needs. This phase requires relatively little active effort if your integrations are connected and your controls are operating correctly. Your main job during this window is monitoring the dashboard for any controls that slip out of compliance and resolving them quickly before gaps widen.
Evidence accumulation is not passive. Reviewing your Vanta dashboard monthly and addressing new failures promptly keeps your audit period clean.
The final push: audit fieldwork and reporting
When your audit period ends, you share auditor access to your Vanta account and your CPA firm begins fieldwork. This phase typically runs four to eight weeks depending on auditor availability and the number of open findings. Responding to auditor questions promptly and resolving any remaining issues quickly shortens this window. Most companies receive their final report within two to three months of fieldwork beginning, completing the full cycle.
Common surprises and how to avoid them
Most teams that go through Vanta SOC 2 compliance for the first time encounter at least one situation they did not anticipate. Knowing where those surprises typically show up lets you prepare for them before they cost you time or delay your audit.
Scope decisions that come back later
One of the most common surprises is discovering that your initial scope definition was too broad or too vague. Teams often include systems loosely connected to customer data without thinking through the implications, which adds controls, evidence requirements, and auditor questions that could have been avoided. Before you finalize your scope inside Vanta, document exactly which systems store, process, or transmit customer data and draw a clear boundary around those. Systems that touch customer data only indirectly often belong outside the audit boundary, and your auditor will accept that argument if you document your reasoning upfront.
Scope creep is easier to prevent at the start than to unwind after your audit period has already begun.
Integrations that do not exist
Vanta covers a wide range of common tools, but not every system your team uses will have a native integration. When a tool lacks a direct connector, you need to upload evidence manually on a recurring schedule throughout the audit period. Teams that discover this late often find themselves scrambling to reconstruct months of manual evidence near the end of the audit window. Audit your full tool stack against Vanta's integration library in your first week of onboarding so you know exactly which systems require manual handling from day one.
Underestimating the human side
The platform automates evidence collection, but it cannot automate employee behavior or process execution. Policies need to be acknowledged, access reviews need to happen on schedule, and security training needs to be completed within the required timeframes. Many teams set up Vanta, connect their integrations, and then neglect the human-dependent controls until an auditor flags them. Assign a single owner to monitor the compliance dashboard on a recurring schedule, at least monthly, and address any controls involving people immediately rather than letting them accumulate into a last-minute remediation push before fieldwork begins.
Next steps
Vanta SOC 2 compliance gives you a structured path through a process that is genuinely complex, but the platform works best when you treat it as a starting point rather than a finish line. Define your audit scope before you connect a single integration, close control gaps in your first 30 days, and assign human-dependent controls to specific owners from day one. Those three steps alone separate teams that finish on schedule from teams that scramble at the end.
If your product touches healthcare data, your compliance requirements extend well beyond SOC 2. HIPAA, EHR connectivity, and secure patient data handling require infrastructure that is built for that environment specifically. SoFaaS runs on SOC 2 Type II compliant infrastructure and handles SMART on FHIR integrations so your team can focus on building rather than managing security and compliance from scratch. See how SoFaaS handles healthcare data integration and decide if it fits what you are building.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.