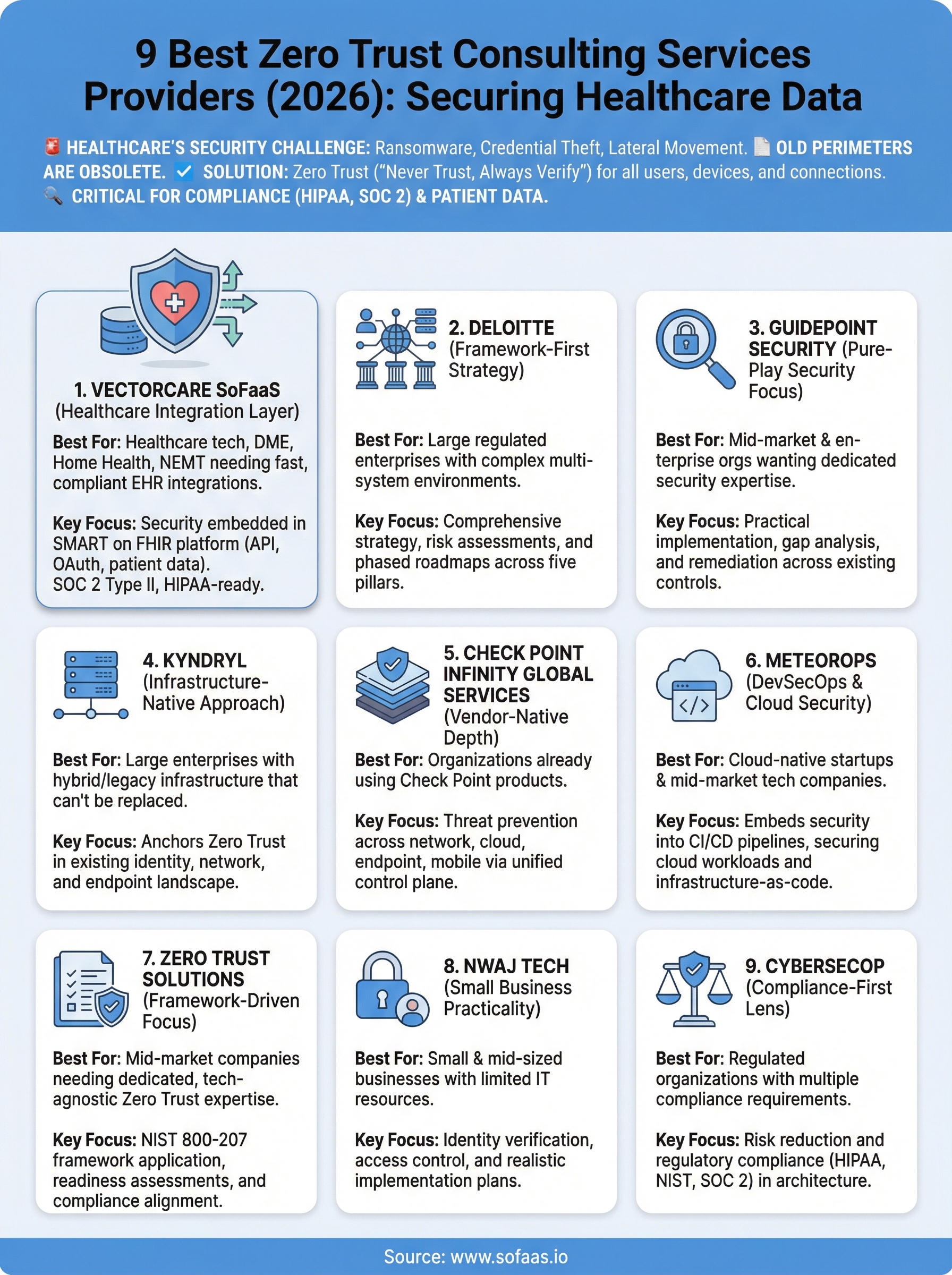
9 Best Zero Trust Consulting Services Providers (2026)


Healthcare organizations handle some of the most sensitive data on the planet, and attackers know it. Ransomware, credential theft, and lateral movement through clinical networks have made traditional perimeter-based security obsolete. That's why more health IT teams are actively searching for zero trust consulting services, expert partners who can help them design and enforce a "never trust, always verify" security model across every user, device, and connection. But choosing the right provider matters, especially when patient data and regulatory compliance are on the line.
At SoFaaS, we build a managed SMART on FHIR integration platform that connects healthcare applications to EHRs like Epic, Cerner, and Allscripts. Security isn't optional in our world, it's foundational. Our infrastructure is SOC 2 Type II compliant and HIPAA-ready by default, with end-to-end encryption and automated authorization management. We work alongside organizations that take zero trust principles seriously, because every API call, every OAuth token exchange, and every patient data sync needs to happen inside a security framework that assumes breach and verifies continuously.
This guide breaks down nine zero trust consulting providers worth evaluating in 2026. We looked at their healthcare experience, technical depth, implementation approach, and ability to support the kind of compliance-heavy environments our customers operate in. Whether you're securing EHR integrations, clinical workflows, or broader enterprise infrastructure, this list will help you find the right consulting partner for the job.
1. VectorCare SoFaaS
VectorCare SoFaaS is built specifically for the healthcare integration layer, the exact place where zero trust principles need to be enforced at the API, OAuth token, and patient data level. Most zero trust consulting services address enterprise IT broadly, but SoFaaS focuses on connecting third-party healthcare applications to EHRs like Epic, Cerner, and Allscripts through the SMART on FHIR standard. Security is embedded in the platform itself, not added as an afterthought.

Zero trust focus and approach
SoFaaS applies a zero trust model at every point in the SMART on FHIR integration stack. Every API call requires authentication, every OAuth token exchange is managed and logged, and all patient data flows through SOC 2 Type II certified, HIPAA-compliant infrastructure. The platform assumes no connection is safe by default, meaning every request is verified continuously regardless of where it originates.
SoFaaS treats every data exchange as a potential threat vector, which is the exact posture zero trust demands.
Typical deliverables
Working with SoFaaS gives you a fully managed integration platform that handles security and compliance from day one. Deliverables include:
- Pre-built EHR connectors for Epic, Cerner, and Allscripts
- Automated OAuth 2.0 token management and patient consent flows
- End-to-end encryption for all data in transit and at rest
- Real-time audit logging to support HIPAA compliance requirements
- Webhook-based patient data sync with a 99.9% uptime SLA
Best for
SoFaaS fits healthcare technology companies, DME providers, home health agencies, and NEMT providers that need fast, compliant EHR integrations without building custom security infrastructure. Your team does not need deep healthcare integration expertise to get started, which makes it practical for organizations under pressure to hit compliance requirements quickly.
Engagement model
The platform runs as a managed service. You connect your application through a single unified API, and SoFaaS handles infrastructure, security operations, and compliance obligations on an ongoing basis. There is no lengthy implementation project, and most teams reach active integration within days of onboarding.
Pricing
Pricing is tiered based on your integration volume and the number of EHR connections your application requires. Visit sofaas.io or contact VectorCare directly to get a pricing estimate matched to your specific deployment and compliance needs.
2. Deloitte
Deloitte is one of the largest professional services firms globally, and their Cyber & Strategic Risk practice brings serious depth to zero trust consulting services. They work across industries but maintain dedicated healthcare and life sciences teams with strong regulatory knowledge built through years of compliance-heavy engagements.
Zero trust focus and approach
Deloitte structures zero trust around five pillars: identity, devices, networks, applications, and data. Their consultants start by mapping your current security posture, then design a phased roadmap that aligns zero trust controls with your business objectives and compliance requirements.
Deloitte's framework-first approach means you get a documented strategy before any technology gets deployed.
Typical deliverables
Their consultants produce zero trust architecture blueprints, risk assessments, and implementation roadmaps tailored to your environment. You also get vendor selection guidance and support for deploying controls across identity platforms, network segmentation tools, and endpoint management systems.
Best for
Large enterprises and regulated healthcare organizations that need a consulting partner with global reach, deep compliance expertise, and the bench strength to handle complex multi-system environments benefit most from Deloitte's model.
Engagement model
Engagements run on a project-based consulting model, typically spanning a few weeks for assessments up to several months for full implementation programs. Deloitte also offers ongoing advisory retainers for organizations that want continuous strategic guidance after initial deployment.
Pricing
Rates are not published publicly. Expect enterprise-level pricing that reflects the firm's scale and specialization. Contact their Cyber & Strategic Risk team directly for a scoped proposal tied to your specific environment.
3. GuidePoint Security
GuidePoint Security is a specialized cybersecurity firm focused exclusively on security consulting and managed security services. Unlike large generalist firms, GuidePoint brings a pure-play security focus to every engagement, meaning their consultants are not splitting attention between business strategy and IT risk. Their zero trust consulting services practice draws on practitioners with hands-on experience deploying controls across complex enterprise environments.
Zero trust focus and approach
GuidePoint builds zero trust programs around practical implementation, not just strategy documents. Their team assesses your existing identity, network, and endpoint controls, then maps out the gaps and builds a prioritized remediation plan. They work with vendors like Microsoft, Palo Alto Networks, and Zscaler to align recommendations with technology you may already have in your environment.
GuidePoint's security-only focus means you get consultants who spend all their time on cybersecurity, not generalists who rotate through practice areas.
Typical deliverables
Engagements typically produce a zero trust maturity assessment, gap analysis, and a phased implementation roadmap. You also get hands-on deployment support for identity governance, network segmentation, and endpoint detection controls, giving you practical help rather than just a report to file away.
Best for
Mid-market and enterprise organizations that want a dedicated security firm rather than a large consulting house benefit most here. Healthcare and financial services companies dealing with strict regulatory requirements and complex vendor environments get strong value from their focused approach.
Engagement model
Their team works on a project-based model for assessments and implementation programs, with options for ongoing managed security services after initial deployment wraps up.
Pricing
Rates are not published publicly. Reach out to their team directly to get a scoped proposal based on your environment size and security maturity, along with the specific controls you need to implement.
4. Kyndryl
Kyndryl is an IT infrastructure services company that spun out of IBM in 2021, and it has quickly established itself as one of the largest independent IT infrastructure services providers in the world. Their security and resiliency practice covers zero trust architecture alongside broader enterprise IT transformation, making them a strong option for organizations that want to modernize infrastructure and security together under one engagement.
Zero trust focus and approach
Kyndryl approaches zero trust consulting services by anchoring every engagement in your existing infrastructure rather than assuming a greenfield environment. Their team assesses your identity systems, network topology, and endpoint landscape before recommending controls, which keeps the roadmap grounded in what you actually have deployed today.
Kyndryl's infrastructure-native approach means their zero trust recommendations account for the complexity of legacy environments that most pure-play security firms overlook.
Typical deliverables
Their consultants deliver zero trust maturity assessments, architecture blueprints, and phased implementation plans designed to fit your existing tooling. You also get hands-on support for deploying controls across identity management, network microsegmentation, and endpoint protection platforms in multi-cloud and hybrid environments.
Best for
Kyndryl fits large enterprises and regulated industries, including healthcare, financial services, and government, that are running hybrid or multi-cloud environments with significant legacy infrastructure that cannot be replaced quickly.
Engagement model
Their team works on project-based and multi-year managed service agreements, depending on your scope and the level of ongoing operational support you need after the initial deployment wraps up.
Pricing
Kyndryl does not publish standard rates. Contact their security and resiliency practice directly to get a scoped proposal based on your environment size and integration complexity.
5. Check Point Infinity Global Services
Check Point is widely known for its network security products, and Infinity Global Services is the consulting and professional services arm that turns that product expertise into hands-on security programs. Their team brings vendor-native depth to zero trust consulting services, which means their consultants understand exactly how Check Point's security stack integrates into a broader zero trust architecture rather than recommending controls in the abstract.
Zero trust focus and approach
Check Point's approach centers on threat prevention across every layer, including network, cloud, endpoint, and mobile. Their consultants use the Infinity architecture to build a unified control plane that enforces consistent zero trust policies across all traffic, reducing the gaps that attackers exploit when security tools operate in silos.
Check Point's strength is connecting security controls across network, cloud, and endpoint into a single enforced policy framework.
Typical deliverables
Their team produces security architecture assessments, zero trust implementation roadmaps, and hands-on deployment support for Check Point's product suite. You also get configuration reviews, policy tuning, and threat prevention hardening across your environment.
Best for
Organizations already running Check Point products get the most value here, since the consulting team can optimize your existing investment rather than rearchitecting from scratch.
Engagement model
Check Point Infinity Global Services offers both project-based engagements for specific deployments and ongoing managed security service agreements for organizations that want continuous monitoring and policy management after initial implementation.
Pricing
Pricing is not listed publicly. Contact their Infinity Global Services team directly to get a scoped proposal based on your environment and product footprint.
6. MeteorOps
MeteorOps is a cloud-focused consulting firm that brings DevSecOps and infrastructure security expertise to zero trust engagements. Their team works primarily with companies running cloud-native or hybrid environments that need security controls built directly into development and deployment pipelines, not added after the fact.

Zero trust focus and approach
MeteorOps applies zero trust principles at the infrastructure layer, focusing on securing cloud workloads, identity access management, and network segmentation across environments built on AWS, Azure, or GCP. Their consultants integrate security controls into your CI/CD pipeline from the start rather than treating security as a separate project phase.
MeteorOps treats infrastructure-as-code as the foundation for enforcing zero trust policies consistently across every environment you deploy.
Typical deliverables
Their team delivers cloud security architecture reviews and zero trust implementation plans with hands-on support for identity and access management controls. Typical outputs include:
- Infrastructure hardening assessments
- Policy-as-code templates for automated deployment workflows
- Identity and access management configuration guidance
Best for
MeteorOps suits cloud-native startups and mid-market technology companies that want zero trust consulting services woven into their engineering workflow. If your team is building on public cloud and wants security embedded in your pipelines, this is a practical fit.
Engagement model
Their team works on project-based engagements for assessments and architecture work, with options for ongoing advisory support after initial delivery.
Pricing
MeteorOps does not publish rates publicly. Contact their team directly to get a scoped proposal tied to your cloud environment and current security maturity.
7. Zero Trust Solutions
Zero Trust Solutions is a consultancy that focuses exclusively on zero trust architecture, making it one of the more specialized options on this list. Their narrow focus means their team spends all of their time on zero trust strategy and implementation rather than spreading attention across broader IT or business consulting topics.
Zero trust focus and approach
Their consultants work from the NIST 800-207 zero trust framework, applying its principles to identity, network segmentation, and data access controls across your environment. Rather than selling you a vendor-specific stack, their team takes a technology-agnostic approach and maps controls to the tools you already have in place before recommending new investments.
Zero Trust Solutions' framework-driven approach gives you a structured blueprint grounded in established standards rather than proprietary methodology.
Typical deliverables
Their team produces zero trust readiness assessments, architecture roadmaps, and implementation guides tailored to your current infrastructure. You also get documentation that your security and compliance teams can use to demonstrate alignment with regulatory requirements like HIPAA or NIST frameworks.
Best for
Organizations that want dedicated zero trust consulting services without bringing in a large generalist firm get the most value here. It works particularly well for mid-market companies that need focused expertise and a clear framework rather than a sprawling multi-year engagement.
Engagement model
Their team works on project-based engagements, covering assessments, architecture planning, and implementation support based on your scope and timeline.
Pricing
Pricing is not listed publicly. Contact their team directly to get a scoped estimate based on your environment and compliance requirements.
8. Nwaj Tech
Nwaj Tech is a small business IT consulting firm focused on cybersecurity and cloud services for small and mid-sized organizations. They bring a practical, hands-on approach to zero trust consulting services, helping smaller teams implement enterprise-grade security controls without the complexity or cost that comes with larger consulting firms.
Zero trust focus and approach
Their consultants structure zero trust work around identity verification and access control, treating every user and device as untrusted until proven otherwise. The team works closely with clients to assess the current security posture and build a realistic implementation plan that fits the budget and technical capacity of smaller organizations.
Nwaj Tech's value is making zero trust accessible to organizations that cannot afford enterprise consulting rates but still face real security threats.
Typical deliverables
Security assessments and zero trust architecture guidance form the core of what Nwaj Tech delivers, all tailored to small business environments. Typical outputs include identity and access management configuration support, network segmentation recommendations, and policy documentation that helps your team maintain controls after the engagement closes.
Best for
Nwaj Tech suits small and mid-sized businesses that need focused zero trust guidance without the overhead of a large consulting firm. Organizations with limited internal IT resources that want practical, implementable advice get strong value from their model.
Engagement model
Their team works on project-based engagements for assessments and implementation support, with options for ongoing managed IT services after the initial work wraps up.
Pricing
Nwaj Tech does not publish standard rates. Contact their team directly to get a scoped proposal based on your organization's size and specific security requirements.
9. CyberSecOP
CyberSecOP is a cybersecurity consulting firm that serves small and mid-sized businesses alongside larger enterprises, with a particular emphasis on managed security, compliance, and risk management. Their team combines advisory services with hands-on implementation support, giving you both the strategy and the technical execution rather than leaving you to bridge the gap yourself.
Zero trust focus and approach
CyberSecOP structures their zero trust consulting services around risk reduction and regulatory compliance, making them a practical option for organizations that need to satisfy frameworks like HIPAA, NIST, or SOC 2 while rebuilding their security architecture. Their consultants assess your current controls across identity, network, and data access before recommending targeted improvements.
CyberSecOP's compliance-first lens means your zero trust roadmap is built with regulatory requirements in mind from the first conversation.
Typical deliverables
Their team provides security risk assessments, zero trust architecture recommendations, and compliance gap analyses as core outputs. You also get policy documentation and implementation guidance that your internal team can use to execute controls after the engagement wraps.
Best for
CyberSecOP works well for organizations in regulated industries that need zero trust guidance paired with direct compliance support. If your security program needs to satisfy multiple regulatory frameworks at the same time, their advisory model covers both objectives in a single engagement.
Engagement model
Their team operates on project-based consulting engagements as well as ongoing managed security service agreements, depending on your internal capacity and how much continuous support your organization needs after initial delivery.
Pricing
CyberSecOP does not publish standard rates. Contact their team directly to get a scoped proposal based on your organization's size, compliance obligations, and current security posture.
Final thoughts
Picking the right zero trust consulting services provider comes down to matching the firm's depth to your specific environment and compliance requirements. Large enterprises running hybrid infrastructure benefit from firms like Deloitte or Kyndryl, while healthcare technology companies with active EHR integration needs should look closely at platforms built with security baked into the integration layer itself.
If your organization builds or manages healthcare applications that exchange patient data with EHRs, security cannot be a separate workstream. Every OAuth token exchange, every API call, and every data sync carries compliance risk that your security architecture needs to address from day one. VectorCare SoFaaS handles that layer for you with SOC 2 Type II and HIPAA-compliant infrastructure built specifically for SMART on FHIR integrations. If you want to see how fast a secure, compliant EHR integration can actually move, explore what SoFaaS can do for your application.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.