What Is Information Blocking? Cures Act Rules & Exceptions


What Is Information Blocking? Cures Act Rules & Exceptions
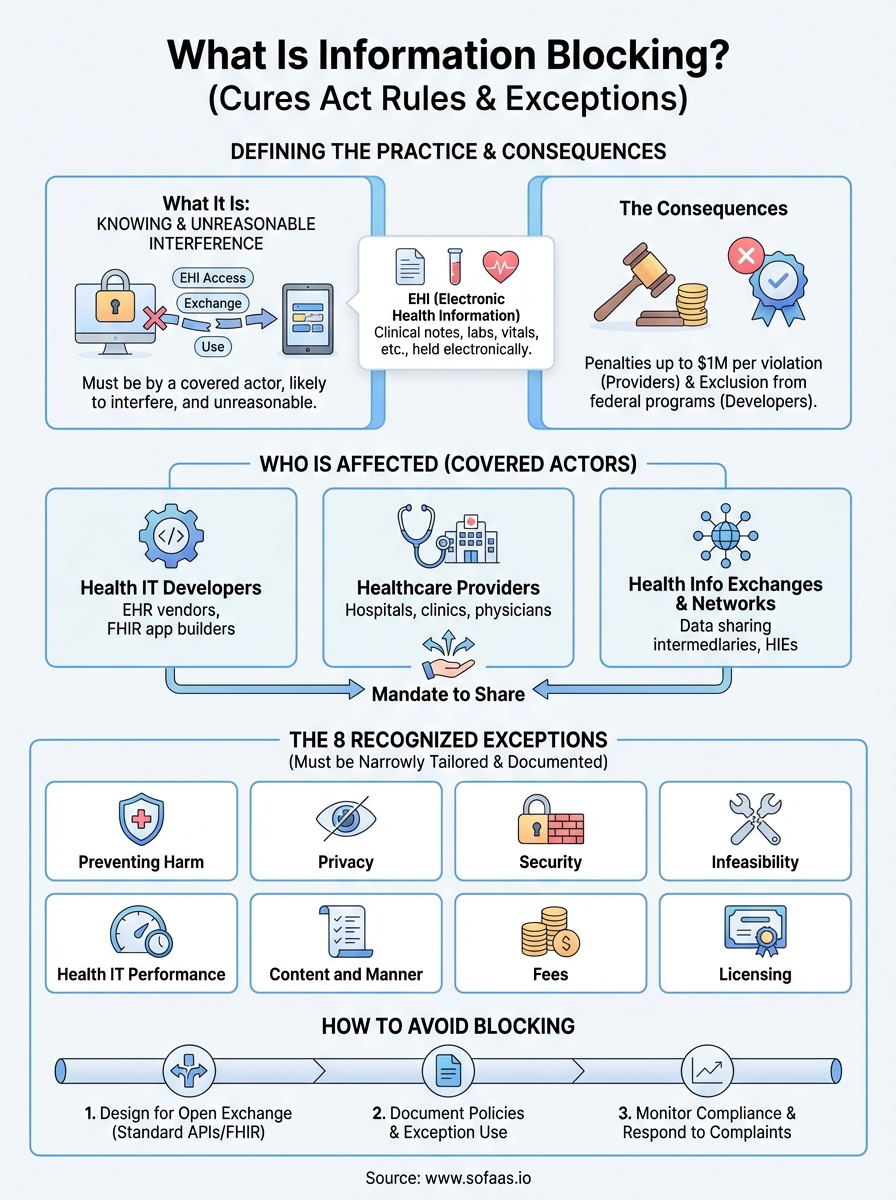
Healthcare organizations and technology vendors are now legally required to share patient data, or face serious consequences. Since the 21st Century Cures Act took effect, understanding what is information blocking has become essential for anyone building or operating healthcare technology. The rules are straightforward: practices that interfere with the access, exchange, or use of electronic health information (EHI) can result in significant financial penalties.
Here's where it gets complicated. The regulations define specific "actors", health IT developers, healthcare providers, and health information networks, each with different compliance obligations. Knowing which rules apply to your organization and what constitutes a valid exception requires careful attention to the details.
This guide breaks down the information blocking regulations, explains who's affected, and outlines the eight recognized exceptions. For healthcare innovators using platforms like SoFaaS to integrate with EHRs via SMART on FHIR, understanding these rules matters, because seamless data sharing isn't just good practice anymore. It's a legal requirement that shapes how you build, deploy, and operate healthcare applications.
What information blocking means under the Cures Act
The Cures Act defines information blocking as any practice that is likely to interfere with the access, exchange, or use of electronic health information. You're engaging in information blocking if you knowingly and unreasonably prevent or materially discourage the sharing of patient data. The law targets behaviors that create barriers to data flow, whether through technical limitations, contractual restrictions, or administrative policies that slow down or prevent legitimate information requests.
The legal definition and scope
Congress designed the information blocking provisions to address a fundamental problem in healthcare: organizations hoarding patient data instead of making it available. The Office of the National Coordinator for Health Information Technology (ONC) established that information blocking occurs when you meet three specific criteria. First, your practice must interfere with access, exchange, or use of electronic health information. Second, the practice must be conducted by a covered actor (health IT developer, healthcare provider, or health information exchange/network). Third, you must know that your practice is unreasonable and likely to interfere with data sharing.
Understanding what is information blocking requires recognizing that intent matters. If you accidentally create a barrier to data sharing, that alone doesn't qualify as information blocking. The regulations focus on deliberate actions that restrict access without a valid reason. For example, if you charge excessive fees for data access, implement technical barriers that serve no security purpose, or use contractual terms that prevent your customers from sharing data with other systems, you're potentially violating the rules.
"The information blocking regulations target knowing and unreasonable practices that interfere with data sharing, not accidental technical failures or legitimate security measures."
What makes a practice information blocking
Three elements must align for your actions to constitute information blocking under federal law. You must be a covered actor subject to the regulations. Your practice must be likely to interfere with the access, exchange, or use of electronic health information, meaning it creates obstacles or discourages parties from requesting or sharing data. Finally, you must act with knowledge that your practice is unreasonable under the circumstances.
The "unreasonable" standard carries significant weight in these determinations. Reasonable practices that serve legitimate business interests, protect patient safety, or maintain system security typically don't qualify as information blocking. However, if you claim security concerns but your restrictions go far beyond what's necessary to protect data, regulators may determine your actions are unreasonable. Similarly, charging fees that exceed your actual costs, requiring unnecessary manual processes when automated solutions exist, or creating preferential treatment for certain partners over others can all trigger information blocking violations.
How the regulations differ from past requirements
Before the Cures Act, healthcare organizations operated under voluntary interoperability frameworks with limited enforcement mechanisms. You could choose which data to share, with whom, and under what conditions. The Meaningful Use program encouraged data exchange through incentive payments, but providers and vendors faced few consequences for restricting information flow. Market dynamics often rewarded data blocking, as organizations used data silos to maintain competitive advantages or lock in customers.
The Cures Act fundamentally changed this dynamic by establishing civil monetary penalties and establishing information blocking as a violation of federal law. Healthcare providers can face penalties up to $1 million per violation, while health IT developers face potential exclusion from federal certification programs. These consequences create real accountability for practices that interfere with data sharing. For organizations building healthcare applications, this shift means you must design systems that facilitate data exchange by default, not restrict it, and document your legitimate reasons for any limitations you implement.
Who the rules apply to and what counts as EHI
The information blocking regulations target three specific categories of organizations called "actors" in the legal framework. If you operate as a health IT developer, healthcare provider, or health information exchange/network, the rules apply directly to your operations. Understanding which category covers your organization determines your specific compliance obligations and the scope of data you must share.
The three types of actors covered
Health IT developers face the strictest requirements under the information blocking rules. You qualify as a health IT developer if you create or supply certified health IT products or systems that store, manage, or transmit electronic health information. This includes EHR vendors, patient portal providers, and application developers who build FHIR-based tools. For platforms like SoFaaS that facilitate EHR connections, understanding what is information blocking matters because you enable data exchange between systems, and your practices must support unrestricted information flow.
Healthcare providers become actors when they control patient data through their clinical operations. If you run a hospital, clinic, physician practice, or any entity that furnishes healthcare services, you fall under these requirements. The regulations don't exempt small practices or specific specialties. Whether you operate a single-physician office or a multi-hospital health system, you must allow patients and authorized parties to access electronic health information without creating unreasonable barriers.
Health information exchanges and health information networks represent the third actor category. You qualify if you operate an organization whose principal purpose is to facilitate information exchange between unaffiliated entities. These organizations serve as intermediaries that connect healthcare providers, payers, and other parties for data sharing. Networks that enable query-based exchange, directed messaging, or centralized data repositories all fall within this definition.
"The three actor categories cover organizations across the healthcare data ecosystem, from those who create systems to those who operate them to those who facilitate connections between them."
What qualifies as electronic health information
Electronic health information extends far beyond traditional medical records. The Cures Act defines EHI as any health information maintained or transmitted electronically, regardless of format, location, or whether it exists in a certified system. This broad definition captures clinical notes, laboratory results, imaging reports, medication lists, immunization records, allergies, vital signs, and demographic data. If you store it electronically and it relates to patient health, it qualifies as EHI.
The scope intentionally avoids technical limitations that previous regulations imposed. You cannot claim that information doesn't qualify as EHI simply because it exists in an older system, uses proprietary formats, or sits outside your certified EHR. Psychotherapy notes documented separately from medical records represent one of the few explicit exclusions, along with information compiled for legal proceedings. Everything else that describes a patient's health status, healthcare provision, or payment for healthcare services falls under the definition and must be accessible without unreasonable interference.
Why information blocking matters in healthcare
The information blocking regulations represent a fundamental shift in how healthcare organizations handle patient data. When you restrict access to electronic health information without a legitimate reason, you create barriers that affect patient outcomes, organizational liability, and the broader healthcare system's ability to deliver coordinated care. The consequences extend beyond regulatory compliance to impact your organization's reputation, financial stability, and ability to participate in value-based care programs.
The patient access implications
Patients experience direct harm when organizations engage in information blocking. When you prevent patients from accessing their own health records, they cannot make informed decisions about their care, verify the accuracy of their medical history, or share critical information with specialists who need it. A patient visiting an emergency room without access to their medication list or allergy information faces increased risk of adverse drug interactions. Similarly, when a patient transfers between healthcare providers, information blocking delays the new provider's ability to understand the patient's history, leading to duplicate testing, treatment delays, and potentially dangerous gaps in care continuity.
Care coordination suffers dramatically when organizations restrict data flow. You limit other providers' ability to deliver effective treatment when you block access to test results, specialist notes, or treatment plans. Patients with chronic conditions who see multiple specialists particularly depend on seamless information exchange. Every barrier you create forces patients to act as intermediaries, manually collecting and transporting paper records between providers, which introduces errors, delays, and frustration that drives patients away from necessary care.
"Information blocking creates fragmentation that forces patients to serve as their own health information exchange, a role they should never need to fill in a modern healthcare system."
The financial and operational risks
Civil monetary penalties create substantial financial exposure for organizations that violate information blocking rules. Healthcare providers face fines up to $1 million per violation, and enforcement agencies can pursue multiple violations for patterns of behavior. Health IT developers risk exclusion from the ONC Health IT Certification Program, which effectively eliminates their ability to sell products to organizations participating in federal programs. Understanding what is information blocking protects your organization from these enforcement actions that can cripple operations and damage market position.
Beyond direct penalties, information blocking creates operational inefficiencies that increase costs across your organization. When you restrict data sharing, you force staff to handle manual records requests, respond to complaints, and manage workarounds that consume administrative resources. These practices also damage relationships with patients, partners, and other healthcare organizations, limiting your ability to participate in care networks, referral partnerships, and collaborative arrangements that drive revenue and improve outcomes.
The information blocking exceptions and when they apply
The ONC established eight specific exceptions that allow you to restrict access to electronic health information without violating information blocking rules. These exceptions protect legitimate interests like patient privacy, system security, and operational feasibility while maintaining the core requirement that you share data unless you have a valid reason not to. You must document your basis for invoking any exception, and your restrictions must be no broader than necessary to achieve the exception's intended purpose.
Understanding the exception framework
You cannot use exceptions as blanket justifications for restricting data access. Each exception includes specific conditions you must meet, and you bear the burden of proving your practices qualify. The regulations require that your restrictions be narrowly tailored to address the legitimate concern the exception protects. For example, if you invoke the security exception to prevent a potential cyber threat, you must show that your response is proportionate to the actual risk and that less restrictive alternatives would not adequately protect your systems.
Misapplying exceptions exposes you to enforcement actions even if you believed your practices were justified. Regulators examine whether you properly assessed the circumstances, implemented the minimum necessary restrictions, and documented your decision-making process. Understanding what is information blocking and its exceptions requires recognizing that these are defensive provisions, not permissions to restrict data flow whenever convenient.
The eight recognized exceptions
The regulations establish distinct categories where you may limit information access. The Preventing Harm exception allows you to restrict data when disclosure would create substantial risk to patient safety. The Privacy exception protects you when sharing would violate federal, state, or tribal privacy laws. You invoke the Security exception when necessary to protect systems from cyber threats or unauthorized access.

The Infeasibility exception applies when technical, legal, or practical obstacles prevent you from fulfilling requests. The Health IT Performance exception covers temporary restrictions during system maintenance or to resolve performance degradation. You use the Content and Manner exception to specify how you provide information, as long as your requirements are reasonable and nondiscriminatory.
The Fees exception permits you to charge for data access, but only at levels that reflect your actual costs to produce and deliver the information. Finally, the Licensing exception protects intellectual property rights when sharing would require disclosing proprietary technology, though it does not excuse you from providing the underlying health information itself.
"The eight exceptions provide legitimate justifications for restricting data access, but only when you apply them narrowly and document your reasoning with evidence that supports the restriction."
When you can invoke these exceptions
You must evaluate each information request individually to determine whether an exception applies. Blanket policies that automatically restrict access rarely qualify, because exceptions require specific circumstances that justify limiting data sharing. For instance, you cannot invoke the Privacy exception to deny all patient requests for their own data, but you can use it to prevent unauthorized disclosure to third parties without proper consent.
Timing matters when you apply exceptions. You must act promptly when legitimate concerns arise, but you cannot maintain restrictions longer than necessary to address the underlying issue. The Security exception might justify temporary suspension of API access during an active cyber attack, but you must restore access once you implement appropriate safeguards and eliminate the immediate threat.
How to avoid information blocking in practice
Avoiding information blocking requires proactive design decisions, clear documentation, and ongoing monitoring of your data sharing practices. You must build systems that facilitate exchange by default rather than requiring patients or providers to navigate barriers you create. Organizations that understand what is information blocking recognize that compliance demands intentional architecture choices and operational procedures that prioritize access over restriction. Your approach should treat data sharing as the standard operating mode, with exceptions applied only when specific, documented circumstances justify them.
Design your systems for open data exchange
You eliminate most information blocking risks by building interoperability into your core system architecture. Implement standardized APIs that follow FHIR specifications and support SMART on FHIR protocols for third-party applications. Your technical design should allow patients and authorized providers to access data through multiple channels, including patient portals, mobile applications, and direct API connections. Platforms like SoFaaS simplify this requirement by providing pre-built connectors that handle the technical complexity of EHR integration while maintaining compliance with information blocking rules.
Your system configuration must avoid creating artificial barriers. Remove unnecessary authentication steps that exceed security requirements, eliminate preferential treatment that grants certain partners faster or easier access than others, and ensure your interfaces respond to requests within reasonable timeframes. Technical restrictions you implement should serve clear security or performance purposes with documented justifications. You protect your organization by making data sharing the default behavior that requires no special approval or manual intervention.
Document your policies and exception use
Written policies create accountability and demonstrate your commitment to information sharing. Establish clear procedures that explain how you handle access requests, what timelines you maintain for responses, and which circumstances trigger exception reviews. Your documentation should specify the person or team responsible for evaluating exceptions and outline the evidence required to justify restrictions. These policies serve as both internal guidance and external proof that you take information blocking obligations seriously.
"Comprehensive documentation proves your organization makes deliberate, justified decisions about data access rather than blocking information through convenience or competitive advantage."
When you invoke an exception, record the specific circumstances, the analysis you conducted, and the minimum necessary restrictions you implemented. This documentation protects you during audits or investigations by showing regulators that you properly applied exceptions according to their intended purpose. Review your documented exceptions regularly to confirm they remain necessary and remove restrictions once the underlying justification no longer applies.
Monitor compliance and respond to complaints
Establish monitoring systems that track access patterns, identify potential blocking behaviors, and flag unusual denial rates or extended response times. Regular audits of your data sharing practices help you catch problems before they become violations. You should review both automated denials and manual access decisions to ensure staff apply exception criteria consistently and appropriately across all requests.
Create straightforward complaint procedures that allow patients, providers, and partners to report suspected information blocking. Respond to these complaints promptly with investigations that determine whether your practices created unreasonable barriers. Fast resolution of legitimate concerns prevents escalation to regulatory enforcement and demonstrates your commitment to compliance.
Key takeaways and next steps
Understanding what is information blocking protects your organization from civil penalties while improving patient care and care coordination. You must share electronic health information unless a specific exception applies, and you bear the responsibility to document your justification when you restrict access. The regulations target three actor categories: health IT developers, healthcare providers, and health information exchanges, each facing distinct compliance obligations that shape how you build and operate systems.
Your immediate action should focus on reviewing your current data sharing practices against the eight recognized exceptions. Examine your technical architecture to ensure you facilitate access through standardized APIs and remove unnecessary barriers that slow or prevent legitimate information requests. If you're building healthcare applications that integrate with EHRs, platforms like SoFaaS handle the technical complexity of SMART on FHIR connections while maintaining compliance with information blocking requirements. Launch your SMART on FHIR app with infrastructure that supports open data exchange by design rather than requiring custom development and ongoing compliance monitoring.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.