What Is Mutual TLS? How mTLS Works and When to Use It


What Is Mutual TLS? How mTLS Works and When to Use It
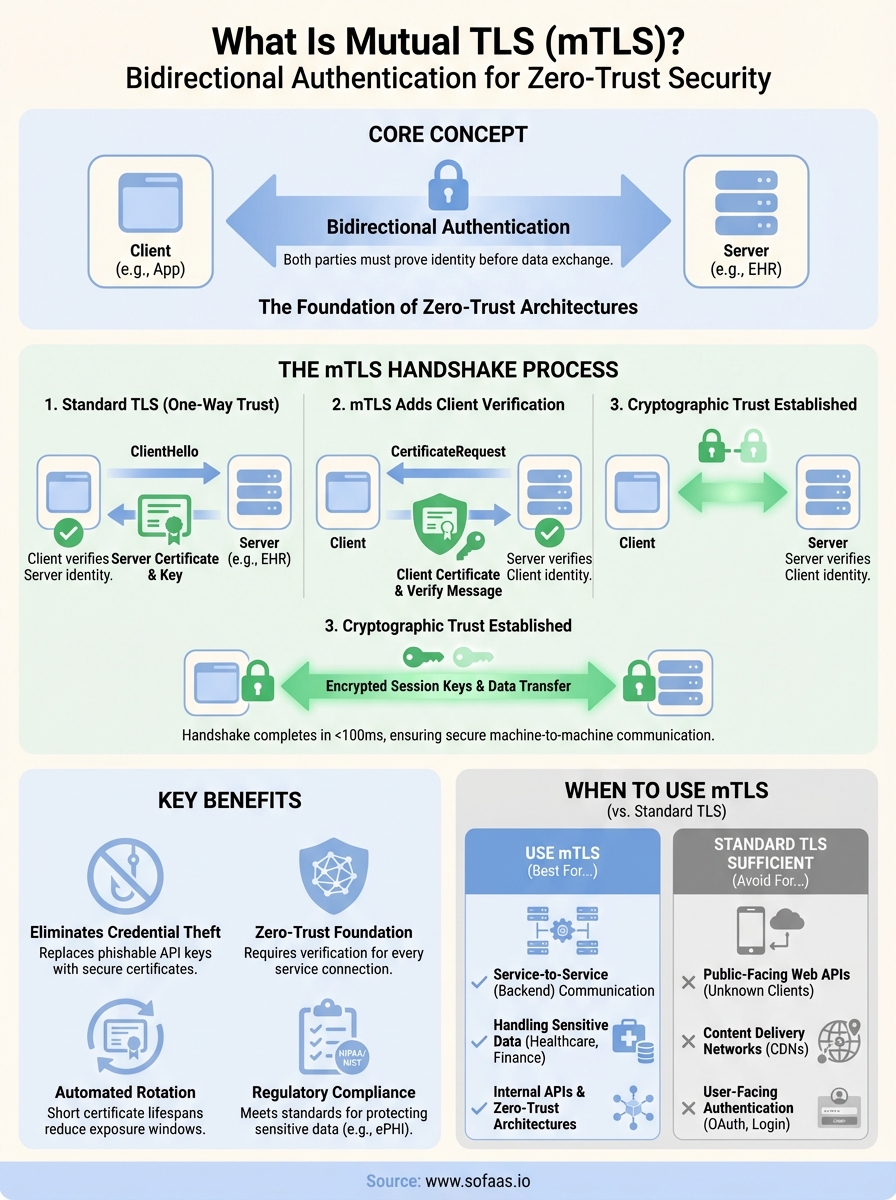
When an API receives a request, how does it know the client is who they claim to be? Standard TLS encrypts traffic and verifies the server's identity, but the client remains essentially anonymous. What is mutual TLS? It's the protocol that closes this gap by requiring both parties to authenticate before any data changes hands.
For organizations handling sensitive information, especially in healthcare where patient data flows between applications and EHRs, one-way trust isn't enough. mTLS adds a second layer of verification, ensuring that the system receiving your API call has proof of your identity, not just the other way around. This bidirectional authentication is why mTLS has become a cornerstone of zero-trust security architectures.
At SoFaaS, we build secure healthcare integrations that connect third-party applications with EHR systems like Epic and Cerner. Understanding mTLS isn't optional when you're moving protected health information, it's foundational. This article breaks down how mutual TLS works, how it differs from standard TLS, and when it makes sense for your infrastructure.
Why mutual TLS matters
Standard authentication methods like API keys and bearer tokens share a critical weakness: they can be stolen, leaked, or replayed by attackers. When your application connects to an EHR system or any external API, you're placing trust in credentials that live in memory, configuration files, or environment variables. A single compromised container or misconfigured storage bucket can expose these secrets to unauthorized parties. What is mutual TLS in this context? It's the shift from "what you know" (passwords, keys) to "what you have" (a cryptographic certificate tied to your identity).
The real cost of compromised service-to-service communication
Healthcare organizations face an average $10.93 million per data breach, according to IBM's 2024 Cost of a Data Breach Report. Most breaches don't start with sophisticated zero-day exploits. They begin when an attacker obtains valid credentials through phishing, insider threats, or exposed API keys in public repositories. Once inside your network perimeter, these credentials grant unfettered access to backend services.
Mutual TLS eliminates this attack vector by requiring certificate-based authentication that can't be guessed, phished, or easily extracted. Even if an attacker intercepts network traffic or gains access to your application logs, they still need the private key associated with your client certificate. This private key typically lives in a hardware security module (HSM) or secure enclave, making extraction orders of magnitude harder than stealing a plaintext API key from an environment variable.
"Certificate-based authentication removes the password problem entirely. You can't phish what doesn't exist."
What regulation actually requires
HIPAA's Security Rule mandates "person or entity authentication" under 45 CFR § 164.312(d). While the regulation doesn't prescribe specific technologies, it requires you to verify the identity of systems accessing electronic protected health information (ePHI). Many organizations interpret this as username/password authentication or API keys, but auditors increasingly expect stronger controls for machine-to-machine communication.
Federal agencies subject to NIST SP 800-53 must implement authenticator assurance levels that often require certificate-based authentication for high-value systems. If you're building healthcare infrastructure that interfaces with government health programs or Veterans Affairs systems, mTLS often becomes a non-negotiable requirement rather than a best practice. The Defense Information Systems Agency (DISA) explicitly mandates mutual authentication for systems processing controlled unclassified information.
When standard authentication breaks down
Token-based authentication assumes you control the entire authentication flow, from initial login to token refresh. This model collapses in distributed systems where services must authenticate to each other without human intervention. You can rotate API keys, but the rotation process itself introduces risk. Someone has to update configuration files, restart services, and hope no requests fail during the transition window.
Mutual TLS provides automatic credential rotation through certificate expiration and renewal. Your infrastructure can enforce short certificate lifespans (hours or days) without the operational overhead of manually updating secrets across your deployment. Certificate authorities can revoke compromised certificates immediately, and systems will reject them on the next connection attempt. This gives you granular control over access that doesn't depend on shared secrets propagating through your infrastructure.
How the mTLS handshake works
Understanding what is mutual TLS requires seeing how the authentication process actually unfolds between client and server. The mTLS handshake extends the standard TLS handshake by adding a second verification step where the server authenticates the client's identity. This bidirectional process happens before any application data moves across the connection, establishing cryptographic trust in both directions.

The initial connection request
When your application initiates a connection to an mTLS-protected endpoint, it first sends a ClientHello message containing supported cipher suites and TLS versions. The server responds with its certificate and public key, just like in standard TLS. Your client verifies the server's certificate against trusted certificate authorities to ensure it's connecting to the legitimate endpoint, not an imposter.
At this point, standard TLS would proceed to establish encryption. Mutual TLS diverges here. The server sends a CertificateRequest message demanding that your client prove its identity. Your application must present its own certificate, signed by a certificate authority the server trusts. Without this client certificate, the handshake fails immediately.
Certificate exchange and validation
Your client transmits its certificate along with a CertificateVerify message that contains a digital signature created with your private key. The server extracts your public key from the certificate and uses it to verify this signature. If verification succeeds, the server confirms you possess the private key corresponding to the certificate you presented, not just a stolen copy of the certificate itself.
The server then checks your certificate against its trust store and certificate revocation lists. It verifies the certificate hasn't expired, the issuing CA is trusted, and the certificate hasn't been revoked. Only after these checks pass does the server accept your identity and proceed with the connection.
"The private key never leaves your system. The server verifies you control it without ever seeing it."
Session key establishment
Both parties now generate session keys using the exchanged public keys and random values from earlier handshake messages. These symmetric keys encrypt all subsequent communication. The entire handshake typically completes in under 100 milliseconds on modern hardware, adding minimal latency while establishing strong mutual authentication that protects every byte of data transferred in the session.
TLS vs mTLS vs HTTPS
These three protocols handle encryption and authentication differently, and choosing the wrong one leaves your infrastructure vulnerable. Standard TLS (Transport Layer Security) encrypts data in transit and verifies the server's identity through certificates. Your browser uses this when connecting to websites. Mutual TLS extends this by requiring both parties to authenticate. HTTPS is simply HTTP wrapped in TLS, the protocol you see in your browser's address bar. Understanding these distinctions helps you select the right security model for your use case.
Standard TLS: Server authentication only
When you connect to a typical web API, standard TLS verifies the server but treats the client as anonymous until application-layer authentication occurs. The server presents its certificate to prove its identity. Your client validates this certificate against trusted certificate authorities and establishes an encrypted channel. After encryption starts, your application sends credentials like API keys or bearer tokens through this secure tunnel.
This one-way authentication model works for public services where the server needs to verify itself to countless unknown clients. Your banking website uses standard TLS because it doesn't need to verify your device cryptographically at the TLS layer. Instead, it handles authentication after the secure connection exists through username and password.
HTTPS: TLS for web traffic
HTTPS simply means HTTP protocol running over TLS. When your browser displays a padlock icon, it confirms the connection uses TLS to encrypt HTTP requests and responses. The server authenticated itself through its certificate, but your browser didn't present any certificate back. This represents the most common implementation of standard TLS on the internet.
Web browsers and public-facing APIs typically use HTTPS because billions of clients need to connect without individual certificate management. You can't issue and manage unique certificates for every person visiting your website.
Mutual TLS: Bidirectional verification
What is mutual TLS compared to these alternatives? It requires certificate-based authentication from both client and server before establishing the encrypted session. Your application must present a valid certificate during the TLS handshake itself, not after. The server validates your certificate against its trust store and rejects connections from clients lacking proper credentials.
"Mutual TLS moves authentication into the TLS handshake, blocking unauthorized connections before they even establish encryption."
This bidirectional model fits machine-to-machine communication where both parties should verify each other's identity cryptographically. Healthcare integrations handling ePHI often mandate mTLS because it prevents unauthorized services from even attempting to authenticate at the application layer.
When to use mTLS and when not to
Choosing between mutual TLS and standard authentication methods depends on who communicates with your system and what data they access. You need mTLS when both parties in a connection must prove their identity cryptographically before exchanging any data. You can skip it when managing certificates for thousands of clients becomes impractical or when your threat model doesn't require bidirectional authentication at the transport layer.
Service-to-service communication scenarios
Deploy mTLS for backend microservices that handle sensitive data and communicate exclusively with known, controlled services. Your payment processing service authenticating to your order management system represents an ideal use case. Both services belong to your infrastructure, you control certificate issuance, and the communication pattern remains predictable. Healthcare integrations between your application and EHR systems demand mTLS because both parties must verify identity before transmitting protected health information.
Internal APIs that access databases containing personally identifiable information benefit from mutual TLS authentication. The overhead of managing certificates for a dozen backend services remains manageable while blocking unauthorized services from even attempting connections. Zero-trust architectures assume breach and require every service to prove its identity, making mTLS the foundation for service mesh implementations like Istio or Linkerd.
"If you control both endpoints and handle regulated data, mutual TLS eliminates the weakest link in your security chain."
When standard TLS remains sufficient
Skip mTLS for public-facing REST APIs where unknown clients need access. A mobile app with thousands of users can't practically manage unique certificates for each device. Standard TLS with OAuth 2.0 or API key authentication handles this scenario better because you authenticate users after establishing the encrypted connection, not during the TLS handshake itself.
Content delivery networks and public documentation sites don't need mutual authentication. Your marketing website receives legitimate traffic from billions of potential visitors. Requiring certificates would block everyone. Understanding what is mutual TLS helps you recognize these boundaries. Use it where you control both endpoints and need cryptographic verification. Avoid it when certificate management overhead exceeds the security benefit or when your client base can't support certificate-based authentication.
How to set up mTLS safely
Setting up mutual TLS requires more planning than standard TLS because you manage certificates for both clients and servers. Your implementation must handle certificate issuance, distribution, rotation, and revocation without creating security gaps or operational nightmares. Understanding what is mutual TLS means accepting that the authentication happens at the transport layer, so your certificate infrastructure becomes critical. A poorly configured setup defeats the entire purpose of bidirectional authentication.
Choose your certificate authority model
You need a certificate authority (CA) to issue and sign certificates for your services. Internal CAs like HashiCorp Vault or AWS Certificate Manager Private CA give you complete control over certificate policies and issuance workflows. You set expiration periods, subject alternative names, and revocation policies without depending on external entities. This model fits organizations where all services exist within your infrastructure boundaries.
Public CAs work when your mTLS implementation spans organizational boundaries or requires third-party auditing. Clients receive certificates from a mutually trusted public authority. The tradeoff involves higher costs and less granular control over certificate lifecycle management compared to running your own CA.
Generate and distribute certificates securely
Generate certificates with private keys that never leave secure storage. Hardware security modules or cloud-based key management services should create and store these keys. Your application accesses the private key through APIs that perform cryptographic operations without exposing the key material itself.
Distribute certificates through automated provisioning systems rather than manual file transfers. Tools like cert-manager for Kubernetes or AWS Secrets Manager inject certificates into your services at deployment time. Short-lived certificates (hours or days) reduce the window of exposure if compromise occurs. Automated rotation prevents outages caused by expired certificates while maintaining security.
"Certificate expiration should trigger automatic renewal, not emergency maintenance windows."
Configure verification policies
Your server must validate incoming client certificates against a trust store containing authorized CA certificates. Configure strict validation that checks certificate expiration, revocation status through CRLs or OCSP, and subject name matching. Reject connections that present valid certificates from untrusted CAs or expired certificates.
Implement certificate pinning for critical connections where you know the expected certificate fingerprint in advance. This prevents attacks where an attacker compromises a trusted CA and issues fraudulent certificates. Your validation logic should log all certificate verification failures for security monitoring and incident response.
Common mTLS failures and fixes
Even properly configured mTLS implementations fail in production due to certificate lifecycle issues, trust chain mismatches, and configuration drift. These failures often surface during high-stakes moments like security audits or when connecting to new partner systems. Understanding what is mutual TLS means anticipating where the bidirectional authentication process breaks down and having fixes ready before your monitoring alerts fire.
Certificate expiration and rotation gaps
Expired certificates represent the most common mTLS failure. Your service presents a certificate that passed its validity period, and the server immediately rejects the connection. This happens when automated renewal processes fail or when manual rotation procedures fall behind schedule. Certificate monitoring tools should alert you at least 30 days before expiration, giving your team time to rotate credentials without emergency maintenance windows.
Fix this by implementing automated certificate renewal through tools like cert-manager or AWS Certificate Manager. Set certificate lifespans to days rather than years, forcing your infrastructure to handle rotation as a normal operation instead of a rare event. Your deployment pipeline should verify that new certificates deploy successfully before marking the rollout complete.
"Treat certificate rotation as a continuous process, not a quarterly task buried in your runbook."
Trust chain validation failures
Your client presents a valid certificate, but the server rejects it because the issuing CA isn't in the server's trust store. This happens when you add a new CA or when certificate chains include intermediate certificates that weren't bundled correctly. Validation fails even though your certificate hasn't expired and your private key remains secure.
Configure your client to send the complete certificate chain, including all intermediate certificates between your client certificate and the root CA. The server must have the root CA certificate in its trust store but shouldn't require you to manually configure intermediate CAs. Test connections against new environments before going live to catch trust store mismatches early.
Subject name and hostname mismatches
Servers validate that the certificate's subject alternative name (SAN) matches the hostname or service identifier in the connection request. Certificates issued for "api.internal.example.com" fail when your client connects using "api.example.com" or the service's IP address. This strict validation prevents man-in-the-middle attacks but causes failures when your DNS configuration changes or when services move between environments.
Request certificates with multiple SANs covering all valid hostnames and service identifiers your clients might use. Include both internal and external DNS names when services need to be accessible from multiple network contexts.
Key takeaways
Understanding what is mutual TLS gives you the foundation to secure service-to-service communication in healthcare infrastructure. Certificate-based authentication eliminates the credential theft vulnerabilities that plague API key and token-based systems. Both parties verify identity before exchanging data, blocking unauthorized connections at the transport layer rather than after establishing encryption.
Implement mTLS when you control both endpoints and handle sensitive data like protected health information. Automated certificate management prevents expiration failures and reduces operational overhead compared to manual rotation processes. Your trust chain configuration must include complete certificate chains and properly configured trust stores to avoid validation failures in production.
Healthcare integrations demand this level of security because compromised credentials cost organizations millions in breach remediation. If you're building applications that connect to EHR systems, launch your SMART on FHIR integration with infrastructure that handles certificate management and compliance requirements from day one.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.