HIPAA Access Control Requirements: Key Safeguards Explained


The HIPAA Security Rule lays out specific standards that covered entities and business associates must follow to protect electronic Protected Health Information (ePHI). Among those standards, HIPAA access control requirements are some of the most operationally demanding, they dictate exactly who can access ePHI, how that access is granted, and what safeguards must be in place to prevent unauthorized exposure. Getting these wrong doesn't just create compliance risk. It creates real patient safety and financial liability.
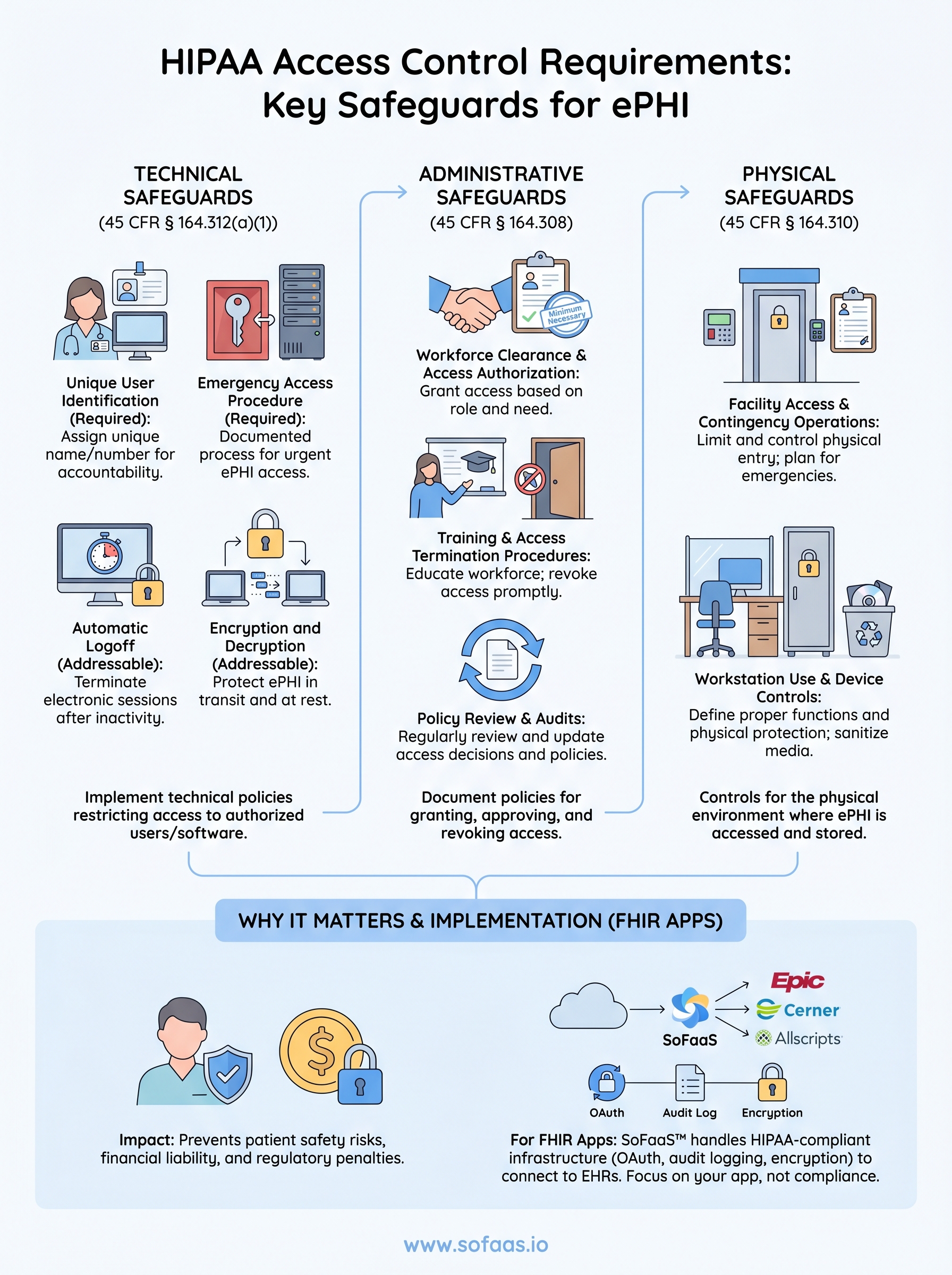
Access control under HIPAA spans both technical and physical domains. It covers everything from unique user identification and emergency access procedures to automatic logoff and encryption. For teams building healthcare applications that connect to Electronic Health Records, these requirements aren't optional boxes to check, they're foundational to how your system must behave from day one. And the complexity compounds fast when you're integrating with multiple EHR systems, each with its own authorization workflows and security expectations.
This is exactly why we built SoFaaS™ (SMART on FHIR as a Service) at VectorCare, to handle the heavy lifting of HIPAA-compliant infrastructure, including OAuth authorization management, audit logging, and encryption, so development teams can focus on their applications instead of compliance plumbing. In this article, we'll break down each access control requirement under the HIPAA Security Rule, explain what it means in practice, and show how these safeguards apply to organizations working with ePHI.
What HIPAA means by access control
The HIPAA Security Rule defines access control under 45 CFR § 164.312(a)(1) as a required standard that covered entities and business associates must implement to allow access to ePHI only by authorized users, programs, or processes. In plain terms, "access control" means having a documented, enforced system that determines who gets in, what they can see, and what actions they can take once they're inside your systems. It's not a single feature or setting. It's a layered set of technical and procedural safeguards that govern the entire lifecycle of ePHI access, from first login to session termination.
Access control under HIPAA isn't just about locking the front door. It's about controlling every room, file, and action inside the building once someone is through it.
The legal definition under the Security Rule
The Security Rule places access control under the Technical Safeguards category, which covers technology and the policies that govern that technology. The standard requires that your organization implement "technical policies and procedures for electronic information systems that maintain ePHI to allow access only to those persons or software programs that have been granted access rights." That wording matters because it puts both human users and software systems in scope. Your application, your integration layer, and your third-party vendor connections all fall under this definition if they touch ePHI in any form.
The rule also distinguishes between required and addressable implementation specifications. Required specifications must be implemented exactly as written. Addressable specifications give you flexibility to implement an equivalent alternative if the original specification isn't reasonable or appropriate for your organization, but you must document your reasoning in writing. Skipping an addressable specification without that documentation is still a compliance violation. Understanding this distinction is foundational when you build out your access control program.
The four implementation specifications
The Security Rule breaks the access control standard into four specific implementation specifications, two required and two addressable. Each one targets a distinct vulnerability in how healthcare systems manage ePHI access:

- Unique User Identification (Required): Assign a unique name or number to each user so you can track and hold individuals accountable for their ePHI activity. Shared credentials violate this specification outright.
- Emergency Access Procedure (Required): Establish documented procedures that allow authorized personnel to access ePHI during an emergency, even when normal access controls are unavailable or bypassed.
- Automatic Logoff (Addressable): Implement procedures that terminate electronic sessions after a defined period of inactivity to prevent unauthorized access on unattended workstations.
- Encryption and Decryption (Addressable): Implement a mechanism to encrypt and decrypt ePHI so that data stays protected both in transit and at rest.
For teams building FHIR-based applications that connect to EHRs, these four specifications map directly onto decisions you make in your authentication layer, your session management logic, and your data storage architecture. Hipaa access control requirements at this level of specificity, broken down specification by specification, are what separate organizations that pass audits from those that face corrective action plans. Each specification is a design constraint, not an afterthought, and your system architecture needs to reflect that from the start.
Why HIPAA access controls matter for ePHI
Electronic Protected Health Information is one of the most targeted data categories in the United States. Healthcare records contain a dense combination of personally identifiable information, insurance details, and medical history that makes them worth significantly more on the black market than credit card data alone. When your organization fails to implement adequate hipaa access control requirements, you expose patients to identity theft, insurance fraud, and long-term harm that goes well beyond a single data breach notification letter.
Unauthorized access to ePHI doesn't just create a compliance problem. It creates a patient safety problem that can follow a person for years.
The financial and legal consequences of access failures
The Office for Civil Rights (OCR) enforces HIPAA and can issue civil monetary penalties that range from $100 to $50,000 per violation, with annual caps reaching $1.9 million per violation category. A single misconfigured access control, such as a shared login credential or an unmonitored third-party integration, can trigger an investigation that results in corrective action plans, mandatory external audits, and years of reporting obligations. The financial exposure scales quickly, especially for organizations managing multiple EHR integrations simultaneously.
Organizations that experience a breach also face mandatory breach notification requirements under 45 CFR § 164.400-414, which means notifying affected individuals, the Department of Health and Human Services, and potentially the media if the breach affects 500 or more individuals in a single state. These notifications carry reputational costs that are harder to quantify but often longer-lasting than the fines themselves.
Why ePHI access requires tighter controls than general IT security
Standard IT security practices protect corporate data, but healthcare data operates under a stricter regulatory framework that demands a higher standard of access governance. ePHI connects directly to clinical decision-making and care delivery, which means unauthorized access can harm a person's health outcomes, not just their financial standing. Your access control architecture needs to account for role-based restrictions and context-sensitive permissions.
Building these controls into a FHIR-based application adds another layer of complexity. Each EHR system has its own authorization configuration, and managing those consistently across Epic, Cerner, and Allscripts requires more than generic security tooling.
HIPAA technical access control requirements
The technical safeguards category is where hipaa access control requirements become the most concrete and measurable. Under 45 CFR § 164.312(a)(1), your organization must implement technical policies and procedures that restrict ePHI access to authorized users and software programs only. This means your application's authentication flow, session logic, and data access layer all carry direct compliance obligations, not just your security policies on paper.
Unique user identification and emergency access
Every person who accesses ePHI must have a unique identifier, whether that's a username, an employee ID, or another individually assigned credential. Shared logins are a direct violation of this required specification because they make it impossible to hold any individual accountable for their actions in the system. Your audit logs become useless if five clinicians share a single account, since you can't trace a specific action back to a specific person when an incident occurs.
Emergency access procedures address a different problem: what happens when normal authentication systems fail during a crisis. Your organization must have documented, tested procedures that allow authorized personnel to retrieve ePHI even when standard login systems are unavailable. This doesn't mean bypassing security entirely. It means defining a controlled exception process with clear authorization steps and post-event audit requirements. Many organizations fail audits on this specification because they have a policy written down but no evidence that anyone has ever tested it.
A documented emergency access procedure that has never been tested is not a functional control. It's a false assurance.
Automatic logoff and encryption
Automatic logoff is an addressable specification, which means you have flexibility in how you implement it, but you still need to implement it or document a justified alternative. In practice, this means configuring sessions to terminate after a defined period of inactivity on any system that can access ePHI. For FHIR-based applications, this includes API sessions and browser-based interfaces alike, not just desktop workstations.
Encryption covers both data in transit and data at rest. Your ePHI must be protected with encryption mechanisms that meet current standards, and your organization must have documented decryption procedures that are accessible to authorized users when needed. Leaving ePHI in plaintext at any point in your data pipeline, even temporarily, creates both a technical vulnerability and a compliance gap.
HIPAA administrative and workforce controls
Technical controls protect your systems, but administrative and workforce controls govern the people who use them. HIPAA's administrative safeguards under 45 CFR § 164.308 require covered entities and business associates to implement documented policies that manage who gets access to ePHI, how that access is approved, and what happens when it needs to be revoked. These policies aren't separate from your technical implementation; they're the governance layer that gives your technical controls their legal standing.
Workforce clearance and access authorization
Your organization must establish a formal process for granting ePHI access that evaluates whether a workforce member's role actually requires that access. This is the principle of minimum necessary access, and it applies directly to hipaa access control requirements at the administrative level. Before someone touches ePHI, you need written documentation showing that their access was reviewed and approved by an appropriate authority within your organization.

Access authorization decisions should map to defined job functions, not individual preferences or convenience. A billing coordinator should not have the same ePHI access as a clinical pharmacist. When you build your authorization matrix, document the reasoning behind each access tier and review those decisions at regular intervals rather than only when a problem surfaces. OCR auditors look specifically for evidence that access decisions are deliberate and revisited over time.
Access that was appropriate when someone was hired may not be appropriate six months later. Reviewing access assignments regularly is not optional, it's an administrative requirement.
Training and access termination procedures
HIPAA requires that your workforce receive security awareness training that covers how to handle ePHI appropriately, including recognizing phishing attempts and following proper access procedures. This training must be documented, and you need records showing who completed it and when. Undocumented training is treated the same as no training during an audit.
Termination procedures carry equal weight. When a workforce member leaves or changes roles, your organization must have a defined, time-bound process for revoking their ePHI access across every system, including third-party integrations and FHIR application credentials. Delays in revoking access after termination are a recurring finding in OCR corrective action plans, and they represent one of the more preventable administrative failures your team can control directly.
HIPAA physical and facility access controls
Physical safeguards under 45 CFR § 164.310 address a dimension of hipaa access control requirements that technical teams often underestimate: the physical environment where ePHI is accessed, stored, and processed. Your servers, workstations, and mobile devices are all in scope, and so are the buildings and rooms that house them. If an unauthorized person can walk up to a terminal or remove a device, your technical controls can be bypassed entirely without any record in your audit logs.
Facility access and contingency operations
Your organization must implement facility access controls that limit physical entry to locations where ePHI systems operate. This means controlled access to data centers, server rooms, and any workspace where ePHI is routinely displayed or processed. Badge readers, key card logs, and visitor sign-in procedures are standard mechanisms, but the requirement goes beyond hardware. You need documented policies governing who is authorized to enter these areas, how authorization is granted, and how access is revoked when someone's role changes.
Physical access logs are just as auditable as digital ones. OCR investigators look at both during a breach investigation.
Contingency operations planning sits alongside facility access under this safeguard. Your organization must document procedures for maintaining physical access to ePHI systems during emergencies such as power failures or building evacuations. This connects directly to the emergency access procedures required under the technical safeguards standard, and the two policies should reference each other explicitly in your compliance documentation.
Workstation use and device controls
Your workstation use policy must define the proper functions for each workstation that accesses ePHI, the manner in which those functions are performed, and the physical attributes of the workstation's surroundings. A laptop in a semi-public clinical area carries different physical risk than a desktop in a locked administrative office. Your policy needs to account for both scenarios with appropriate physical controls such as privacy screens, cable locks, and clear-desk procedures.
Device and media controls extend this requirement to cover how your organization handles hardware when it's moved, repurposed, or disposed of. Sanitization procedures for storage media that held ePHI must be documented and followed without exception, and you need records showing those procedures were actually carried out.
How to implement HIPAA access controls for FHIR apps
Building a FHIR application that satisfies hipaa access control requirements demands more than selecting a compliant hosting provider and calling it done. Your authentication layer, authorization scope configuration, session management, and audit infrastructure all need to work together from the start, because EHR integrations expose ePHI the moment they establish a connection. Every design decision you make in your application's data flow carries a compliance implication.
Map your authorization layer to FHIR scopes
SMART on FHIR uses OAuth 2.0 scopes to define exactly what patient data your application can read or write during an authorized session. These scopes are your primary technical mechanism for enforcing minimum necessary access at the API level. If your application only needs to read a patient's medication list, your scope request should reflect that rather than requesting broad read access across all clinical resources. Requesting wider scopes than your application requires is a direct conflict with the principle of least privilege that underpins HIPAA's access control standard.
Your scope configuration also needs to align with the role-based access policies you've documented in your administrative safeguards. A patient-facing application and a clinician-facing application should request different scopes and authenticate through separate credential flows. Building this separation into your architecture early prevents the kind of over-provisioned access that triggers corrective action plans after an audit.
The SMART on FHIR authorization model gives you the tools to enforce minimum necessary access at the API level. Use them with the same rigor you apply to your internal access control policies.
Automate audit logging and session management
Every ePHI access event in your FHIR application must be logged with enough detail to reconstruct exactly who accessed what data, from which system, and at what time. Your logs need to capture user identity, resource type, timestamp, and the action taken. Storing those logs in a tamper-resistant, encrypted format is what makes them useful during an OCR investigation rather than just a performance artifact in your infrastructure stack.
Session management requires automatic timeout enforcement on every interface that surfaces ePHI, including API tokens and browser-based views. Configure token expiration windows that reflect your clinical use case, and build token refresh logic that re-validates authorization before extending a session rather than simply issuing a new token on demand.
Key takeaways and next steps
HIPAA access control requirements touch every layer of your healthcare application, from the OAuth scopes you request during a FHIR authorization flow to the badge logs outside your server room. The four technical implementation specifications, unique user identification, emergency access procedures, automatic logoff, and encryption, form the foundation, but they only hold up when your administrative policies and physical safeguards reinforce them consistently. Gaps at any layer create the kind of exposure that OCR investigations are built to find.
Building all of this from scratch while also shipping a competitive healthcare application is a significant resource commitment. SoFaaS handles HIPAA-compliant OAuth management, audit logging, encryption, and EHR-specific authorization configuration so your team can focus on application development rather than compliance infrastructure. If you're ready to connect your application to Epic, Cerner, or Allscripts without rebuilding the compliance stack yourself, launch your SMART on FHIR app with SoFaaS and get connected in days, not months.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.