Twilio HIPAA BAA: Eligibility, Covered Products, And Cost


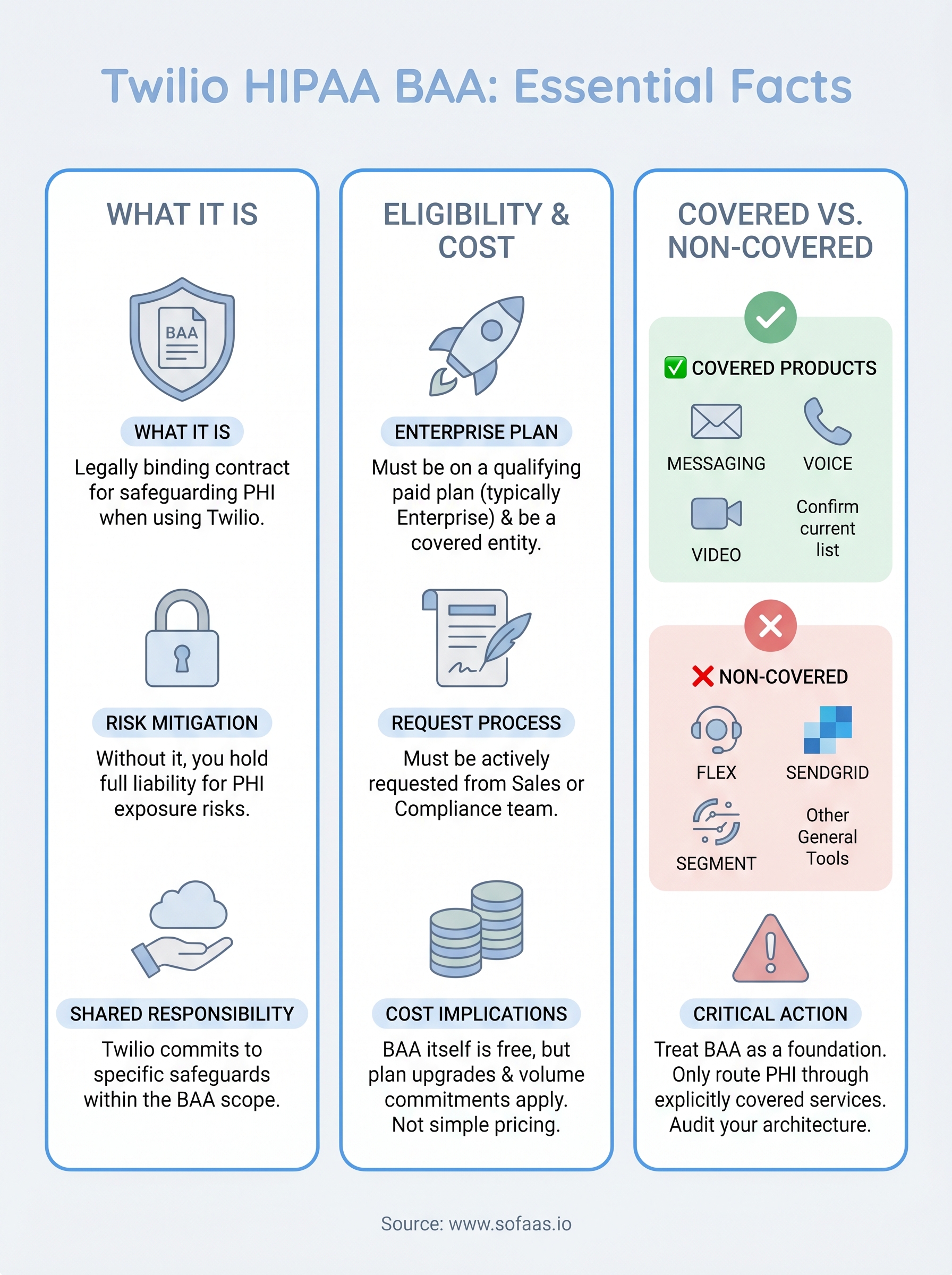
If you're building a healthcare application that uses Twilio for messaging, voice, or video, you can't just flip a switch and start transmitting protected health information (PHI). You need a Twilio HIPAA BAA, a Business Associate Agreement that legally binds Twilio to safeguard any patient data flowing through its services. Without one, you're exposed to serious regulatory risk, regardless of how secure your app might be on the technical side.
Getting a BAA signed is one piece of the compliance puzzle, but understanding which Twilio products it actually covers, what it costs, and whether your account even qualifies, that's where most teams hit friction. The requirements aren't always obvious, and Twilio's documentation spreads the details across multiple pages.
This article breaks down everything you need to know: eligibility criteria, covered products, pricing implications, and the steps to get your BAA in place. At SoFaaS, we help healthcare teams handle the compliance-heavy parts of EHR integration, including HIPAA-compliant infrastructure and data flows, so we understand how critical it is to get every vendor agreement right before PHI touches your stack.
What a Twilio HIPAA BAA is
A Business Associate Agreement is a legally binding contract required under HIPAA whenever a covered entity, such as a hospital, health plan, or healthcare clearinghouse, shares protected health information with a third-party vendor. When you transmit patient data through Twilio's infrastructure, Twilio qualifies as a business associate under HIPAA, which means you must have a signed BAA in place before any PHI flows through their systems. The agreement outlines the specific obligations Twilio accepts for safeguarding that data and the conditions under which it can be used or disclosed.
The Legal Foundation Behind the Requirement
HIPAA's Privacy Rule and Security Rule don't just regulate how your organization handles PHI; they extend to every vendor that processes that data on your behalf. If you skip the BAA and PHI passes through Twilio anyway, you and your organization carry the full liability for that exposure. The Department of Health and Human Services can issue civil penalties ranging from hundreds to millions of dollars per violation category, depending on the level of negligence the investigation uncovers.
Signing the Twilio HIPAA BAA does not make your entire implementation HIPAA compliant; it means Twilio accepts shared responsibility for protecting PHI within the defined scope of the agreement.
What the Agreement Obligates Twilio to Do
The BAA specifies that Twilio will implement appropriate administrative, physical, and technical safeguards to protect PHI processed through their covered services. It also requires Twilio to report any security incidents or breaches involving your data within a defined timeframe. These obligations mirror what HIPAA demands from covered entities themselves, giving you a documented paper trail that proves your vendor relationships meet regulatory standards.
The agreement also restricts how Twilio can use PHI. They cannot use patient data for their own business purposes, such as product improvement or analytics, without your explicit authorization. This boundary is one of the core protections the twilio hipaa baa provides, and you should read it carefully rather than treating it as a standard checkbox item. Understanding exactly what Twilio commits to, and what it does not, shapes how you architect the rest of your HIPAA-compliant communication stack.
Who is eligible and how to request it
Not every Twilio account qualifies for a BAA. Eligibility is tied to your subscription tier, and Twilio only executes the agreement with organizations on specific paid plans. If you're operating on a free trial or a standard pay-as-you-go account, you cannot access the twilio hipaa baa process until you upgrade to a qualifying tier.
Eligibility Requirements
Twilio requires that you be on an Enterprise plan or a qualifying paid tier before they will execute a BAA. Your organization must also function as a covered entity or a business associate under HIPAA, meaning you handle PHI in the course of delivering a healthcare service or supporting one. Individual developers or non-healthcare companies building general-purpose applications do not qualify, even if they happen to process some health-related data.
Twilio's BAA is not automatically attached to your account when you upgrade; you must actively request it through their compliance process.
Steps to Request the BAA
Your first step is to contact Twilio's sales or compliance team directly, either through the Enterprise contact form on their website or via your assigned account representative if you already have one. You will need to provide details about your use case, confirm your plan tier, and agree to Twilio's compliance terms. The review process can take several business days, so build that timeline into your launch schedule rather than treating it as a last-minute task.

Once your BAA is executed, Twilio will attach it to your account and document the covered services. Keep a copy on file for your own compliance records, since auditors may request evidence of your vendor agreements during a HIPAA review.
Which Twilio products the BAA can cover
Twilio does not extend the twilio hipaa baa to every product in its catalog. The agreement covers a defined subset of services, and you need to confirm that the specific products your application uses are included before you transmit any PHI. Using a non-covered Twilio product to handle patient data, even accidentally, creates a compliance gap that the BAA cannot fix retroactively.

Core Eligible Services
Twilio's BAA typically covers Programmable Messaging, Programmable Voice, and Programmable Video as the foundational services most healthcare applications depend on. These products handle the actual transmission of communication content, which is where PHI most commonly appears in healthcare workflows such as appointment reminders, telehealth calls, and patient notifications.
Confirm the exact list of covered products with your Twilio account representative, since Twilio updates its BAA scope periodically and documentation can lag behind current policy.
Services That Are Not Covered
Several popular Twilio products fall outside the BAA's coverage, and this is where many development teams run into trouble. Twilio Flex, SendGrid, and Twilio Segment are examples of services that are either excluded entirely or require separate agreements. If your application routes PHI through any of these tools, you carry the compliance risk without Twilio's contractual protection.
Review your full integration architecture before executing the BAA. Map every point where patient data could touch a Twilio service, then verify each one against the covered products list. If a service you depend on is not covered, you have three options: switch to a covered alternative, remove PHI from that workflow entirely, or find a separate HIPAA-compliant vendor for that function.
How to use Twilio with PHI safely
Signing a twilio hipaa baa does not automatically make your implementation safe. The agreement defines Twilio's obligations, but your development and configuration choices determine whether PHI is actually protected in practice. Treat the BAA as a foundation, not a finish line.
Restrict PHI to Covered Services Only
Route patient data only through the Twilio services explicitly listed in your BAA. If you use a non-covered product even briefly in a workflow that touches PHI, you create a compliance gap that the signed agreement cannot close. Audit your integration architecture regularly to catch any new services or changes that could introduce a non-covered channel.
When you build new features, validate each Twilio service against your covered products list before writing production code that processes patient data. Building that checkpoint into your development review process is far less expensive than discovering a gap during a regulatory audit or breach investigation.
The BAA protects you only within the boundaries of what it explicitly covers, so your architecture must enforce those same boundaries at the code level.
Configure Access Controls and Logging
Twilio provides account-level security features such as API key scoping, sub-account isolation, and access control lists that you should configure before any PHI touches their services. Limit API credentials to the minimum permissions required for each function, and store keys in a dedicated secrets manager rather than in environment variables or source code.
Audit logging is equally important. Twilio's account logs capture API activity, but you should also implement logging on your own infrastructure to record when PHI enters and exits Twilio's services. Regulators expect a clear, timestamped record of how patient data moves through your system, and gaps in that record complicate any investigation significantly.
Cost, pricing, and hidden expenses
Accessing the twilio hipaa baa is not a standalone purchase, but it carries real costs that most teams underestimate when budgeting for compliance. The agreement itself is available at no separate fee, but you must be on a qualifying Enterprise plan to request it, and that plan upgrade comes with its own pricing structure that can significantly increase your monthly Twilio spend.
Plan Upgrade Costs
Twilio's Enterprise pricing is negotiated directly with their sales team rather than published on a standard pricing page, which means you won't find a simple number to plug into your budget spreadsheet. Enterprise contracts typically include volume commitments and minimum spend thresholds, so you need to forecast your messaging, voice, and video usage carefully before signing. Under-estimating usage can leave you locked into a plan that costs more than the value you extract from it.
Request a detailed breakdown of all contract terms before committing, including overage rates that apply when your usage exceeds the plan's committed volume.
Hidden Expenses to Watch For
Beyond the plan cost, several indirect expenses add up during a HIPAA-compliant Twilio deployment. Implementing proper access controls, audit logging, and sub-account isolation requires engineering time that is easy to overlook in project estimates. If your architecture routes data through any non-covered Twilio products, you may also need to pay for separate HIPAA-compliant alternatives to fill those gaps. Factor in ongoing maintenance and periodic compliance reviews as well, since your configuration will need revisiting any time Twilio updates its covered products list or your application adds new communication workflows.
Key Takeaways and Next Steps
The twilio hipaa baa gives you a legal foundation for transmitting patient data through Twilio's platform, but it only protects the services explicitly named in the agreement. You need an Enterprise-tier account to access it, and you must actively request it rather than wait for it to appear automatically. The BAA covers a specific subset of Twilio products, so map your entire integration architecture before signing and confirm every service your application touches appears on the covered products list.
Your compliance stack rarely stops at a single vendor agreement. If your healthcare application also needs to integrate with EHR systems and handle patient data across multiple touchpoints, the engineering complexity compounds quickly. SoFaaS handles the heavy lifting on the EHR integration side, including HIPAA-compliant infrastructure and pre-built connectors for Epic, Cerner, and Allscripts, so your team can focus on building the application rather than managing compliance. Start your SMART on FHIR integration and reduce your time to launch.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.